Delving into Router & Switch, we explore the backbone of modern networking. Understanding how these devices function and their roles […]
Freyablog
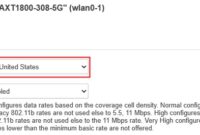
5g Network
Exploring the 5G Network unveils a groundbreaking chapter in telecommunications, where speed meets innovation in ways previously unimaginable. The advent […]
Fiber Optics
Fiber Optics is revolutionizing the way we communicate, transmit data, and interact with the world around us. As technology evolves, […]
Embedded Systems
Embedded Systems are the unsung heroes of modern technology, seamlessly integrating into our daily lives and revolutionizing the way devices […]
Internet Of Things (Iot)
Internet of Things (IoT) is transforming the way we interact with the world around us, creating an interconnected ecosystem that […]
Edge Computing
As Edge Computing takes center stage, this technology is reshaping the way we process data and interact with the digital […]
Server Farm
Server farms are essential hubs in today’s digital landscape, housing numerous servers that work together to manage, store, and distribute […]
Quantum Computing
Quantum Computing represents a monumental shift in how we process information, leveraging the bizarre principles of quantum mechanics to solve […]
Motherboard
Motherboard serves as the fundamental backbone of any computer system, connecting all components and allowing them to communicate seamlessly. It’s […]
5g Network
Jaringan 5G telah menjadi sorotan utama dalam perkembangan teknologi komunikasi modern, menghadirkan kecepatan dan efisiensi yang belum pernah ada sebelumnya. […]