Virtual Private Network (VPN) technology has become an indispensable tool in today’s digital landscape, where online privacy is continually threatened. With increasing cyber threats and data breaches, having a VPN is like securing a digital fortress around your personal information. It offers users a safe passage through unsecured networks, shields them from prying eyes, and enables access to restricted content. Imagine browsing the internet freely, without the fear of your data being intercepted or misused; this is the promise of a VPN. As we delve deeper into the world of VPNs, you’ll discover how they work, their various types, and why they’re essential for anyone looking to enhance their online security.
From understanding the risks of using public Wi-Fi to exploring how VPNs encrypt your data, this guide aims to equip you with knowledge about the importance and functionality of Virtual Private Networks. With this understanding, you’ll be better prepared to make informed choices about your online activities and privacy.
The importance of using a Virtual Private Network for online security
In today’s digital age, the significance of online privacy cannot be overstated. With increasing amounts of personal data being shared online, users face a constant threat to their information. A Virtual Private Network (VPN) plays a crucial role in enhancing online security by encrypting internet traffic and masking the user’s IP address, thereby providing a layer of protection from potential threats.
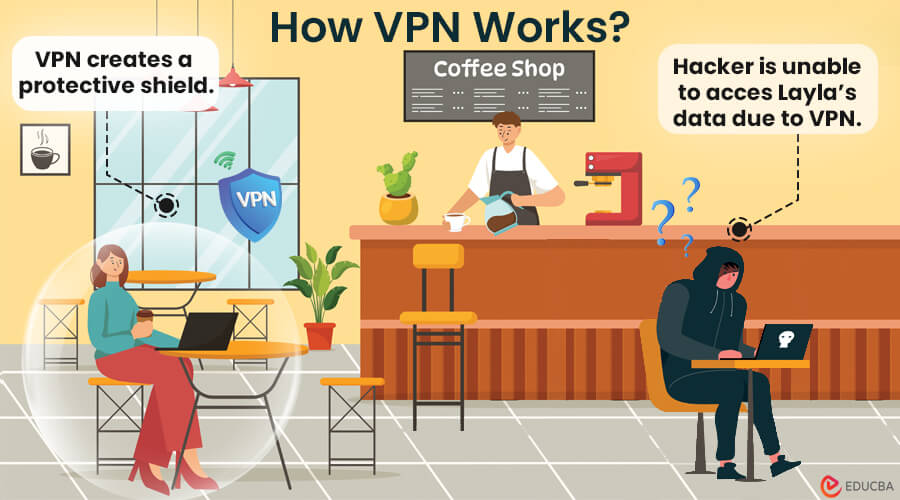
The risks associated with unsecured internet connections are numerous and can have severe consequences. When users access the internet without the protection of a VPN, their data can easily be intercepted by malicious actors. This is especially prevalent in scenarios where users connect to public Wi-Fi networks, which are often unsecured. In such cases, hackers can employ various techniques, including man-in-the-middle attacks, to capture sensitive information such as passwords, credit card numbers, and personal messages. A VPN mitigates these risks by encrypting the data transmitted over the internet, making it nearly impossible for outsiders to decipher the information. The encryption process creates a secure tunnel for the user’s data, ensuring that even if it is intercepted, it remains unreadable.
Public Wi-Fi usage
Using a VPN is particularly critical when connecting to public Wi-Fi networks, which are commonly found in cafes, airports, and hotels. These networks often lack sufficient security measures, leaving users vulnerable to data breaches. A VPN enhances security in such environments by providing encryption and anonymity, thereby shielding personal information from prying eyes.
Consider the following scenarios illustrating the need for a VPN while using public Wi-Fi:
- Accessing online banking: When checking bank accounts or conducting transactions on public Wi-Fi, a VPN ensures that sensitive financial data is protected from potential theft.
- Sharing sensitive documents: Professionals who need to send or receive confidential files over a public network can utilize a VPN to secure their communications and maintain privacy.
- Streaming content: When connecting to public Wi-Fi to stream videos, a VPN can prevent data throttling and provide access to geo-restricted content while keeping the user’s browsing activity private.
A VPN not only protects individual users but also contributes to broader online security by fostering a culture of privacy awareness. By utilizing a VPN, individuals can take proactive steps to safeguard their information, ensuring a safer, more secure online experience. In an era where data breaches are becoming increasingly common, adopting a VPN is not just a wise choice but a necessary one for maintaining online privacy.
How Virtual Private Networks work to encrypt data
Virtual Private Networks (VPNs) play a crucial role in enhancing online security by encrypting data transmitted over the internet. This process involves converting readable data into an unreadable format, ensuring that unauthorized individuals cannot access or interpret it. The encryption mechanisms employed by VPNs safeguard user information from potential cyber threats, enhancing privacy while browsing or using online services.
VPNs primarily leverage encryption algorithms to protect data. When a user connects to a VPN, their internet traffic is routed through a secure tunnel created by the VPN server. This tunnel uses cryptographic protocols to encrypt the data, rendering it secure from eavesdroppers. The encryption process transforms plain text into cipher text, which can only be decrypted by someone possessing the correct encryption key.
Commonly used encryption protocols in VPN services
Understanding the various encryption protocols that VPNs implement is essential, as they significantly impact the security and performance of the VPN service. The following are widely used protocols, each with unique features:
- OpenVPN: An open-source protocol that is highly configurable and uses robust security features. It supports various encryption algorithms, offering versatility and strong protection.
- IKEv2/IPsec: Known for its speed and stability, especially on mobile devices. It combines IKEv2 for the secure key exchange and IPsec for encrypting the data.
- L2TP/IPsec: This VPN protocol combines Layer 2 Tunneling Protocol with IPsec, providing a higher level of security than L2TP alone, but can be slower due to double encapsulation.
- WireGuard: A newer protocol praised for its simplicity and efficiency. It offers high-speed connections and strong encryption, often making it faster than older protocols.
The implementation of these encryption protocols ensures that users’ data remains confidential. For instance, consider a user accessing a public Wi-Fi network at a coffee shop. Without VPN encryption, a hacker could easily intercept data transmitted over the network, potentially gaining access to sensitive information like passwords or personal messages. However, with a VPN, this data is encrypted, safeguarding it from prying eyes.
As a result, encrypted data significantly protects user information against various threats, including identity theft, data breaches, and unauthorized surveillance. The assurance of privacy provided by VPN encryption empowers users to browse the internet with confidence, knowing that their data is secure and protected from potential cyberattacks.
Different types of Virtual Private Networks and their uses
Virtual Private Networks (VPNs) are essential tools for ensuring secure and private internet connections. They are widely utilized to protect sensitive data and enhance online privacy across different environments. Understanding the distinct types of VPNs available can help individuals and organizations choose the right solution to meet their unique needs.
VPNs can be categorized mainly into two types: remote-access VPNs and site-to-site VPNs. Each serves its purpose effectively in both personal and business contexts, offering different functionalities based on user requirements.
Remote-Access VPNs
Remote-access VPNs enable individual users to connect securely to a private network from a remote location, such as their home or while traveling. This type of VPN is commonly used by telecommuters or individuals who need to access company resources while away from the office.
Some specific use cases for remote-access VPNs include:
– Employees accessing company files and databases securely from home.
– Travelers connecting to their home network to access local content.
– Users maintaining privacy on public Wi-Fi networks by encrypting their internet traffic.
Site-to-Site VPNs
Site-to-site VPNs function differently by connecting entire networks to one another, allowing multiple users at different locations to communicate securely. This setup is typically used by businesses with multiple offices or branches that need to share data across locations without exposing it to potential threats.
Use cases for site-to-site VPNs include:
– Corporations linking remote offices to the main headquarters to allow seamless internal communication.
– Businesses integrating networks of different locations for collaborative projects.
– Organizations merging networks during acquisitions or partnerships for secure data sharing.
Comparison Table
To provide a clearer understanding of the differences between remote-access and site-to-site VPNs, the following table Artikels their key features:
| Feature | Remote-Access VPN | Site-to-Site VPN |
|---|---|---|
| User Level | Individual users | Entire networks |
| Primary Use | Secure connection for remote access | Linking multiple networks |
| Configuration Complexity | Relatively simple | More complex due to multiple devices |
| Security | High encryption for individual sessions | Secured inter-network communication |
| Common Use Cases | Telecommuting, secure browsing | Corporate networking, data sharing between branches |
The role of Virtual Private Networks in bypassing geographical restrictions

In our increasingly connected world, access to online content is often limited by geographical restrictions, commonly referred to as geo-blocking. This practice affects streaming services, websites, and various online applications, causing frustration for users who wish to access content that is available in other regions. Virtual Private Networks (VPNs) play a pivotal role in overcoming these barriers, allowing users to browse the internet freely as if they were in a different location.
Geo-blocking can significantly impact online activities, limiting users from accessing essential services, entertainment, or vital information based on their physical location. For instance, streaming platforms like Netflix, Hulu, or BBC iPlayer often have different libraries of content available in various countries. This restriction can hinder users’ experiences, forcing them to miss out on popular shows or even critical news content that may not be available in their region. VPNs address this issue effectively by masking the user’s actual IP address, making it appear as if they are accessing the internet from a different location. As a result, users can enjoy unrestricted access to their desired content, regardless of their geographical location.
Legal implications and responsibilities of using a VPN
While VPNs provide a robust solution for bypassing geo-restrictions, it is crucial for users to understand the legal implications and responsibilities associated with their use. Many streaming services and websites have terms of service that prohibit accessing their content through VPNs. Engaging in such practices may lead to the suspension of accounts or legal action, depending on the jurisdiction.
Users must also recognize that while VPNs can provide anonymity and privacy, they are not a blanket shield against all legal repercussions. For example, in countries where internet censorship is prevalent, using a VPN to access banned content can still lead to significant legal consequences. Therefore, it is important for users to stay informed about the laws regarding VPN usage in their region as well as the terms of service of the platforms they wish to access.
Overall, while VPNs serve as a powerful tool for accessing geographically restricted content, users must balance this advantage with an understanding of the potential legal ramifications and personal responsibilities that come with circumventing geo-blocking measures. It is essential to use VPNs ethically and in accordance with applicable laws to maintain a safe and compliant online experience.
Evaluating Virtual Private Network providers for reliability and performance
When considering a Virtual Private Network (VPN) provider, reliability and performance are paramount in ensuring a secure and smooth online experience. Selecting the right VPN involves evaluating several important criteria, each playing a critical role in the overall effectiveness of the service. By assessing these factors, users can make informed decisions that align with their needs for privacy, security, and internet freedom.
The primary criteria for selecting a trustworthy VPN provider include security protocols, server locations, connection speeds, privacy policies, and customer support. Each of these elements contributes to the service’s overall reliability and performance. Security protocols like OpenVPN and IKEv2 ensure robust encryption, vital for protecting sensitive data. A diverse range of server locations allows users to access geo-restricted content while optimizing connection speeds.
When evaluating connection speeds, it’s crucial to consider factors such as latency and bandwidth, as these directly affect streaming and browsing experiences. Privacy policies should be transparent, clearly outlining whether the provider logs user data, which is essential for maintaining anonymity. Lastly, quality customer support can be a lifesaver when technical issues arise, ensuring minimal disruption to service.
Comparison of Popular VPN Providers
Below is a comparative table showcasing key features, pricing, and user ratings of some popular VPN providers. This highlights the strengths and weaknesses of each to aid in decision-making.
| VPN Provider | Features | Pricing | User Rating |
|---|---|---|---|
| ExpressVPN | High-speed servers, strong encryption, no logs | $12.95/month | 4.7/5 |
| NordVPN | Double VPN, CyberSec, over 5400 servers | $11.95/month | 4.6/5 |
| Surfshark | Unlimited devices, CleanWeb, MultiHop | $2.49/month | 4.4/5 |
| CyberGhost | User-friendly, dedicated streaming servers | $2.75/month | 4.3/5 |
| Private Internet Access | Robust privacy features, ad-blocking | $2.85/month | 4.5/5 |
The importance of customer support and user experience cannot be overstated in the selection process. A responsive support team ensures that users can quickly resolve issues that may arise, enhancing the overall experience. Additionally, an intuitive user interface is crucial; a well-designed application allows for seamless navigation and usability across devices.
User reviews and ratings often provide insight into the reliability of customer service and the overall user experience, making them an essential consideration when choosing a VPN provider. The combination of robust customer support and an easy-to-navigate interface significantly contributes to the reliability and effectiveness of a VPN service.
Common misconceptions about Virtual Private Networks
Many people hold misconceptions about Virtual Private Networks (VPNs), which can lead to misunderstandings about their capabilities and importance. These misunderstandings can hinder users from effectively protecting their online privacy and security. By clarifying these myths, we can better appreciate the value of VPNs in today’s digital landscape.
One prevalent misconception is that VPNs provide complete anonymity online. While it’s true that VPNs can mask your IP address and encrypt your internet traffic, they do not make you fully anonymous. Your online activities can still be tracked through methods such as cookies, browser fingerprints, and behavior tracking by websites. Moreover, if a user accesses their accounts without additional privacy measures, their identity can still be exposed.
Another myth is the belief that all VPN services offer the same level of protection. In reality, VPNs vary widely in quality and features. Some may log user data, have weak encryption, or lack sufficient security measures to protect against cyber threats. Choosing a reputable VPN provider is crucial for ensuring robust security.
Additionally, there is a misconception that using a VPN significantly slows down internet speed. While it’s true that VPNs can add some latency due to encryption processes, many high-quality VPNs are designed to maintain fast speeds. Users often report minimal differences in speed, especially when connecting to a VPN server that is geographically close.
Misinformation surrounding VPNs can lead to users underestimating their importance. Some users might avoid using VPNs entirely due to these myths, leaving them vulnerable to data breaches, privacy invasions, and other online threats. For instance, a company that neglected to implement VPN for remote employees experienced a significant data breach, exposing sensitive client information. Their failure to educate staff on using VPNs resulted in severe financial and reputational damage.
Understanding the facts about VPNs is essential for safeguarding your online presence.
In summary, addressing these misconceptions and spreading factual information about VPNs can empower users to make informed decisions about their online security and privacy.
Future trends in Virtual Private Network technology
As technology evolves, so too does the landscape of Virtual Private Networks (VPNs). The future of VPN technology is likely to be shaped by advancements in encryption, user demands for privacy, and the increasing prevalence of cyber threats. Understanding these trends can help users make informed decisions about their online security and privacy.
Emerging trends suggest that VPN technology will not only become more accessible but also more essential in our daily digital interactions. With the rise of remote work and global connectivity, VPNs are becoming a staple for personal and professional use. Users will increasingly demand faster, more reliable connections without sacrificing privacy. Moreover, as governments and corporations continue to implement data restrictions and surveillance protocols, the need for robust VPN solutions will grow. This shift will likely lead to new, innovative features aimed at enhancing user experience and security.
Advancements in encryption methods
The future of VPNs will heavily rely on advancements in encryption technologies. Current standards, like AES-256 encryption, are considered highly secure, but researchers are continually seeking improvements. Future VPN services may adopt quantum-resistant encryption methods, which would protect data against the potential threats posed by quantum computing.
Moreover, the implementation of machine learning algorithms in encryption could lead to more adaptive security measures. These advancements could analyze user behavior to provide tailored security protocols that evolve in real-time. This means that users can expect a higher level of personalization in their VPN services, as well as stronger safeguards against emerging cyber threats.
Anticipated features in new VPN offerings
As VPN technology progresses, certain features are expected to become standard in new offerings. These anticipated features will cater to the evolving needs of users seeking enhanced privacy and convenience.
- Multi-hop connections: This feature routes user traffic through multiple servers, adding layers of security and making it harder for third parties to trace online activity.
- Split tunneling: Users will be able to choose which traffic goes through the VPN and which goes directly to the internet, optimizing speed and performance for specific applications.
- Improved user interfaces: Future VPNs will likely offer more intuitive interfaces, making it simpler for users to manage their security settings and connection preferences.
- Better performance and speed: With technological advancements, users can expect faster connection speeds without compromising encryption strength, making the user experience smoother.
- Integrated ad and tracker blocking: Many new VPNs may come with built-in features that block ads and tracking scripts, providing users with a more private browsing experience.
- Cross-platform support: Enhanced interoperability across devices and operating systems will likely be a standard offering, ensuring users can maintain security regardless of their chosen device.
These anticipated developments not only highlight the direction VPN technology is heading but also reflect the growing emphasis on user-centric features aimed at enhancing privacy, speed, and convenience in the online space.
Conclusive Thoughts
In conclusion, Virtual Private Networks (VPNs) are not just a luxury but a necessity in our connected world. Whether you’re trying to secure your online activity on public Wi-Fi or accessing geo-restricted content, VPNs provide a crucial layer of protection and freedom. As technology evolves, so do the capabilities and importance of VPNs, making it essential to stay informed about the latest developments and trends. By understanding how to choose a reliable provider and recognizing common misconceptions, you can confidently navigate the digital space while keeping your personal information safe and secure.
FAQ
What is a Virtual Private Network (VPN)?
A VPN is a service that creates a secure connection over the internet, allowing users to browse privately and access content safely.
How does a VPN protect my data?
It encrypts your internet traffic, making it unreadable to anyone who tries to intercept it.
Can I use a VPN on my mobile device?
Yes, most VPN services offer apps for mobile devices, ensuring security on the go.
Are all VPNs the same?
No, VPNs vary in features, pricing, and performance, so it’s essential to choose one that fits your needs.
Is using a VPN legal?
Generally, yes, but using a VPN to engage in illegal activities is against the law.
Will a VPN make my internet slower?
While there might be a slight decrease in speed due to encryption, high-quality VPNs minimize this impact significantly.
Can a VPN help me bypass internet censorship?
Yes, VPNs can help you access content that is blocked or restricted in certain regions.
Do I need a VPN for online banking?
While not mandatory, using a VPN can add an extra layer of security for online banking activities.
How do I know if a VPN is trustworthy?
Look for reputable providers with a transparent privacy policy, strong encryption, and good customer reviews.