Ransomware has transformed from a niche cyber threat to a pervasive issue that affects individuals and organizations worldwide. This malicious software encrypts files, demanding payment for access, and its evolution over the years showcases an alarming trajectory of increasing sophistication and impact. As we explore the history, mechanics, and consequences of ransomware, we uncover not only its technical aspects but also the profound effects it has on victims and the broader implications for society.
From its humble beginnings in the late 1980s to the complex and varied forms seen today, ransomware has continuously adapted to evade detection and enhance its effectiveness. Understanding its evolution helps us grasp the current landscape of cybersecurity challenges and the pressing need for robust defenses against this ever-evolving threat.
Ransomware Overview and Its Evolution
Ransomware has evolved into one of the most formidable threats in the cybersecurity landscape. Initially emerging in the late 1980s, it has undergone significant transformations, adapting to technological advancements and the growing sophistication of cybercriminals. Understanding its historical context provides valuable insights into its current manifestations and the ongoing battle against it.
The first known instance of ransomware can be traced back to 1989, when a computer scientist named Joseph Popp released the “AIDS Trojan.” This malware was distributed via floppy disks and would encrypt the names of files on the infected computer. Users were then prompted to send a payment to a post office box in Panama in exchange for a decryption key. Though rudimentary by today’s standards, this marked the inception of ransomware as a means of extorting victims.
As technology advanced, so did the complexity and prevalence of ransomware. The early 2000s saw a surge in ransomware variants, often leveraging email as a distribution method. Notable milestones include the emergence of the “Gpcoder” and “Archievus” ransomware in the mid-2000s, which targeted Windows operating systems and demanded payment in online currency. The introduction of more sophisticated encryption methods marked a significant turning point, enabling attackers to hold files hostage effectively.
In 2013, the emergence of CryptoLocker was a watershed moment in the evolution of ransomware. Utilizing strong encryption algorithms, CryptoLocker would encrypt user files and demand a ransom payable in Bitcoin. This marked the beginning of the “ransomware-as-a-service” model, where attackers could easily deploy ransomware for a fee, significantly increasing the number of cybercriminals engaging in this illicit market.
Today, ransomware has diversified into several distinct types, each exhibiting unique characteristics. The most common include:
Types of Ransomware
Ransomware can be classified into various categories based on their operational mechanisms and tactics. Understanding these types is essential for effective prevention and response strategies.
- Encrypting Ransomware: This type encrypts files on the victim’s system, making them inaccessible until a ransom is paid. CryptoLocker and WannaCry are prime examples.
- Locker Ransomware: Unlike encrypting ransomware, locker ransomware locks users out of their devices, preventing access to the operating system. Examples include the Police Trojan, which masquerades as law enforcement.
- Scareware: This variant primarily relies on fear tactics, often falsely claiming that the victim’s system is infected or illegal activity has been detected. It demands payment to resolve the purported issue.
- Ransomware-as-a-Service (RaaS): This model allows cybercriminals to rent ransomware for a cut of the profits. It has democratized ransomware attacks, enabling less skilled individuals to join the cybercrime landscape.
Each type of ransomware presents distinct challenges for victims and cybersecurity professionals alike, highlighting the importance of robust security measures and awareness in combating this pervasive threat.
The Mechanics of Ransomware Attacks
Ransomware attacks have become one of the most pressing cybersecurity threats in recent years, impacting individuals and organizations alike. Understanding the mechanics behind these attacks is crucial for developing effective defenses and response strategies. This discussion dives into how ransomware infiltrates systems, the encryption process it employs, and the lifecycle of an attack from initial breach to data recovery.
Infiltration Methods of Ransomware
Ransomware typically infiltrates systems through various methods, exploiting vulnerabilities and human behavior. Common techniques used by attackers include phishing emails, malicious attachments, and compromised software downloads. Phishing emails often masquerade as legitimate communications, enticing the recipient to click on a link or download an attachment that contains the ransomware payload. Attackers may also use social engineering tactics, leveraging urgency or fear to prompt users to take actions that compromise their security.
Another prevalent method is the exploitation of software vulnerabilities. Attackers scan for unpatched software on devices, using exploit kits to gain access to the system. Once in, they can deploy the ransomware payload, initiating the attack. In recent years, Remote Desktop Protocol (RDP) brute-force attacks have also gained traction, where hackers systematically guess passwords to access networks and install ransomware directly.
Encryption Process of Ransomware
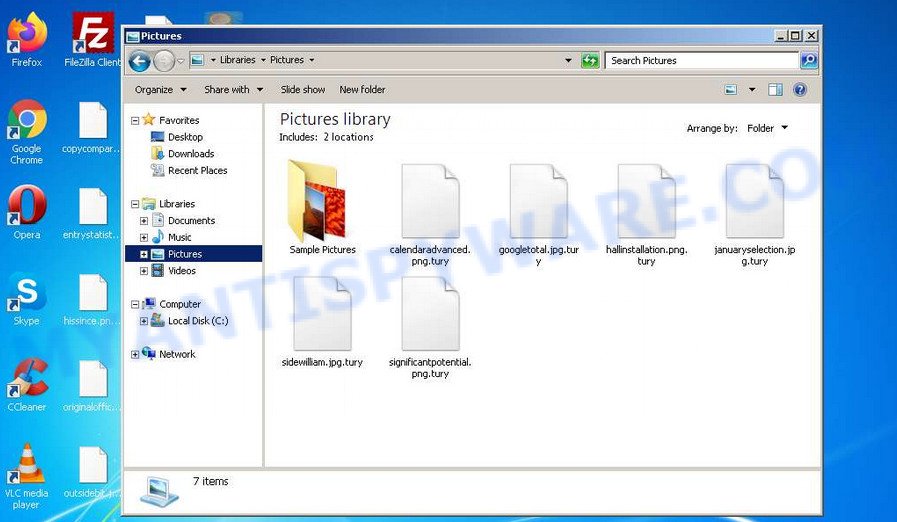
Once ransomware infiltrates a system, it begins its encryption process, which is the cornerstone of its attack. The ransomware identifies files that it deems valuable, such as documents, images, and databases, and encrypts them using strong encryption algorithms. The encryption process is rapid, often completing within minutes to evade detection. For instance, many ransomware variants utilize AES (Advanced Encryption Standard) encryption, which provides robust security that is nearly impossible to break without the decryption key held by the attackers.
The impact of encryption on the victim’s data is profound. Encrypted files become inaccessible, rendering them unusable. Victims typically encounter messages demanding a ransom payment in exchange for the decryption key. The ransom amounts can vary significantly, often ranging from hundreds to millions of dollars, depending on the perceived value of the data and the target’s ability to pay. Attackers often employ a double-extortion tactic, threatening to publish sensitive data if the ransom is not paid, further increasing pressure on the victims.
Lifecycle of a Ransomware Attack
Understanding the lifecycle of a ransomware attack provides insights into the stages that victims experience from the moment of breach to potential data recovery. The lifecycle generally unfolds in several key stages:
1. Initial Breach: This is the entry point where attackers gain access to the system through one of the aforementioned methods. Early detection is critical at this stage to prevent further infiltration and damage.
2. Deployment: Once access is achieved, the ransomware is deployed within the network. This often includes lateral movement, where the ransomware spreads to other systems to maximize its impact.
3. Execution and Encryption: The ransomware executes and starts encrypting files. During this stage, users may notice system slowdowns as processes are hijacked by the ransomware.
4. Ransom Demand: Following encryption, the ransomware displays a ransom note, informing the victim of the situation and detailing how to pay the ransom. This stage is often accompanied by threats regarding data exposure.
5. Negotiation and Payment: Victims may engage in negotiations with the attackers, though paying the ransom does not guarantee the return of data, as perpetrators may not provide a decryption key or may demand additional payments.
6. Data Recovery: In the aftermath, organizations may choose to restore their data from backups if available, or seek assistance from cybersecurity professionals to recover files. However, the impact of the attack can linger, including reputational damage and financial losses.
“Ransomware attacks are not just about encryption; they are a multi-faceted threat that can severely disrupt operations and damage trust.”
Impact of Ransomware on Businesses and Individuals
Ransomware attacks have become increasingly prevalent, posing significant challenges for both organizations and individuals. The ramifications of such attacks extend beyond immediate financial losses, affecting operational capabilities and emotional well-being. Understanding the breadth of these impacts is crucial for stakeholders in developing effective prevention and response strategies.
Financial and Operational Consequences of Ransomware
Ransomware infections can severely disrupt the normal operations of an organization, leading to considerable financial ramifications. The immediate cost of a ransomware attack often includes the ransom itself, which can range from a few hundred to millions of dollars, depending on the size of the organization and the sensitivity of the data targeted. For instance, a notable attack on Colonial Pipeline in May 2021 resulted in a ransom payment of $4.4 million, leading to significant operational disruption in one of the United States’ largest fuel pipelines.
Organizations also face costs related to recovery efforts, including IT forensics, data recovery, and system restoration. The downtime caused by such attacks can result in lost productivity, with some estimates suggesting that businesses can lose thousands of dollars per hour during outages. In addition, there are often indirect costs such as reputational damage, loss of customer trust, and potential legal liabilities, which can have long-lasting effects on a company’s bottom line.
“The average cost of a ransomware attack for a mid-sized company is estimated to be over $1.85 million, factoring in ransom payments, downtime, and lost revenue.”
Moreover, businesses may also incur additional expenses related to cybersecurity enhancements post-attack to prevent future incidents, leading to a compounding effect on their financial health.
Emotional and Psychological Effects of Ransomware
The emotional and psychological toll of ransomware attacks on victims is profound, affecting both individuals and businesses. Victims often experience feelings of fear, anxiety, and helplessness as they grapple with the implications of their data being compromised. For businesses, this stress can be exacerbated by concerns over potential job losses, regulatory scrutiny, and damage to their brand reputation.
Individuals may feel violated and anxious about personal data breaches, leading to long-term distrust in digital platforms. The psychological impact can result in a state of hyper-vigilance, where victims become overly cautious about their online activities, significantly affecting their digital lifestyle and productivity.
Notable Case Studies and Long-Term Repercussions
Examining notable ransomware attacks can provide insights into the long-term repercussions faced by targeted entities. The 2017 WannaCry attack, which affected over 200,000 computers worldwide, highlighted vulnerabilities in many organizations, including the NHS in the UK. The attack resulted in cancelled medical procedures and a loss of trust in healthcare IT systems, the effects of which lingered for years as organizations scrambled to bolster their defenses.
Another significant case is the attack on the city of Baltimore in 2019, which crippled municipal operations for weeks. The city refused to pay the ransom, leading to recovery costs exceeding $18 million, alongside the costs of rebuilding affected systems. The long-term consequences also included a continued struggle with cybersecurity investments and a heightened awareness of vulnerabilities among city officials.
These case studies illustrate that the impact of ransomware is not merely a momentary disruption but can lead to ongoing financial burdens and shifts in operational practices, making cybersecurity a priority for organizations and individuals alike.
Prevention Strategies for Ransomware Attacks

Ransomware attacks pose a significant threat to both individuals and organizations. Implementing effective prevention strategies is crucial to safeguard sensitive data and ensure operational continuity. By actively addressing vulnerabilities and promoting awareness, the risk of falling victim to ransomware can be substantially reduced.
To combat ransomware effectively, individuals and businesses can adopt a variety of strategies that focus on technical measures, user education, and policy implementation. The following table Artikels key preventive measures alongside their best practices.
| Preventive Measure | Best Practices |
|---|---|
| Regular Software Updates | Ensure all software, including operating systems and applications, are up-to-date to mitigate vulnerabilities. |
| Backup Data Frequently | Implement a routine backup schedule, storing data offline or using secure cloud solutions to restore information in case of an attack. |
| Use Strong Security Software | Deploy comprehensive antivirus and anti-malware solutions that include ransomware protection features. |
| Limit User Privileges | Restrict administrative rights for users and implement the principle of least privilege to limit access to sensitive data. |
| Email Filtering and Security | Utilize advanced email filtering solutions to block phishing attempts and malicious attachments that often spread ransomware. |
Cybersecurity Training for Employees
Regular cybersecurity training is essential for equipping employees with the knowledge to recognize and respond to ransomware threats effectively. By fostering a culture of security awareness, businesses can significantly reduce the likelihood of successful attacks.
Training programs should focus on the following key areas:
- Identifying Phishing Attempts: Teach employees how to recognize suspicious emails and links that may lead to ransomware downloads.
- Safe Browsing Practices: Instruct staff on safe internet usage, highlighting the risks associated with downloading software from untrusted sources.
- Reporting Protocols: Establish clear guidelines for reporting potential security incidents, ensuring timely responses to threats.
- Regularly Scheduled Drills: Conduct simulated phishing attacks and incident response drills to reinforce training and gauge employee awareness.
- Updates on Emerging Threats: Keep employees informed about the latest ransomware trends and tactics to help them stay vigilant.
“An informed employee is the first line of defense against ransomware attacks.”
Recovery from Ransomware Attacks
Experiencing a ransomware attack can be a daunting and overwhelming situation for individuals and organizations alike. The immediate steps taken post-attack are crucial in determining the extent of the damage and the effectiveness of the recovery. Following a structured approach to recovery can mitigate losses and restore normal operations more swiftly.
After discovering a ransomware attack, the first action should be to isolate the infected systems immediately. Disconnecting affected devices from the network prevents the ransomware from spreading to other machines. Next, assess the damage by determining which files are locked or encrypted and identifying the type of ransomware involved. This information is essential for recovery decisions and potential interaction with cybersecurity professionals. It’s also vital to communicate the incident to relevant stakeholders, including IT personnel, management, and possibly law enforcement, depending on the severity of the attack.
Once the initial response is executed, organizations should consider the recovery strategies available. If a reliable backup system is in place, it can help restore data lost to the ransomware. This highlights the importance of a robust backup strategy, which should include regular backups stored securely and offsite. Effective backup solutions enable quick restoration of data without the need to engage with the ransom demands. These backups should be tested periodically to ensure data integrity and availability when needed most.
Role of Cybersecurity Professionals in Recovery
Cybersecurity professionals play a pivotal role in the recovery process after a ransomware attack. Their expertise encompasses a range of activities aimed at securing the environment and preventing future incidents. Engaging cybersecurity experts can provide organizations with a thorough forensic analysis of the attack, enabling them to understand the vulnerabilities that were exploited. This analysis is crucial for strengthening defenses and thwarting future attempts.
Additionally, cybersecurity professionals assist in the recovery phase by advising on the best practices for data restoration from backups. They can guide organizations on how to safely eliminate the ransomware from affected systems to prevent further loss or compromise. Their involvement also includes assessing the overall security posture post-incident and recommending improvements to policies, user training, and technology solutions.
In summary, the swift and systematic recovery from ransomware attacks hinges on immediate response actions, the implementation of resilient backup strategies, and the expert guidance of cybersecurity professionals. Each of these components is vital in not only recovering lost data but also in fortifying defenses against potential future attacks.
Legal and Ethical Considerations Surrounding Ransomware
Ransomware attacks pose significant challenges not only in terms of cybersecurity but also from legal and ethical perspectives. Organizations faced with the dilemma of paying ransoms must navigate a complex landscape of laws, regulations, and moral obligations. The repercussions of these actions can be far-reaching, influencing not only the immediate situation but also future organizational policies and legal standings.
Legal Implications of Paying Ransoms
The decision to pay a ransom is fraught with legal implications that organizations must carefully consider. In many jurisdictions, paying ransoms may inadvertently support criminal enterprises. This can lead to allegations of complicity with organized crime, exposing organizations to legal liabilities. For instance, the U.S. Treasury Department has issued guidance cautioning entities against paying ransomware demands, especially if the payments go to individuals or groups listed on sanctions lists.
Organizations might face severe penalties if it is found that they have inadvertently funded terrorist activities or other illicit operations. Additionally, there are potential ramifications regarding insurance claims; some insurers may refuse to cover ransom payments, viewing them as a violation of policy terms. This can leave organizations in a precarious financial situation if they have relied on insurance to mitigate losses from cyberattacks.
Moreover, companies that disclose ransomware payments might face scrutiny from regulators and stakeholders, impacting their reputation and trustworthiness. Publicly traded companies, in particular, can encounter shareholder lawsuits if they fail to disclose material risks associated with cyber threats.
Furthermore, legal frameworks surrounding data breaches, such as GDPR in Europe, impose stringent notification requirements on organizations that may be forced to disclose breaches if personal data is compromised. This can lead to additional penalties, further complicating the decision-making process regarding ransom payments.
Ethical Dilemmas in Ransom Payments
Beyond the legal perspective, the ethical considerations of paying ransomware demands present a challenging dilemma for businesses. Companies may grapple with the moral implications of funding criminal behavior, as paying ransoms can perpetuate the cycle of cybercrime. By giving in to demands, organizations risk encouraging future attacks, potentially harming others in their industry.
The ethical approach also involves weighing the impact on employees, customers, and other stakeholders. Organizations may feel a responsibility to protect sensitive data and minimize business disruption, leading to a temptation to comply with the attackers’ demands. However, this can conflict with the principle of not rewarding criminal behavior.
To navigate these ethical waters, businesses might consider rigorous risk assessments and developing comprehensive incident response plans that include alternative strategies to ransomware payments. This approach allows organizations to prioritize stakeholder interests while also standing firm against cybercriminals.
Law Enforcement Perspectives on Ransomware
Law enforcement agencies globally take a firm stance against ransomware attacks, recognizing their growing prevalence and sophistication. Many agencies, such as the FBI and Europol, advocate for not paying ransoms as it only feeds the ecosystem of cybercrime. They emphasize the importance of reporting such incidents to facilitate investigations and potentially identify attackers.
Agencies employ a range of strategies to combat ransomware, including public awareness campaigns, providing resources for prevention, and developing frameworks for rapid response. Law enforcement collaborates with private sector entities to improve threat intelligence sharing, allowing for a more coordinated approach to tackling ransomware threats.
In some cases, law enforcement has even managed to recover ransom funds through various means, including tracing cryptocurrency transactions and executing coordinated takedowns of ransomware infrastructure. This proactive stance underscores the importance of collective efforts in addressing the threat of ransomware and protecting businesses from cybercriminal exploitation.
The Future of Ransomware and Cybersecurity
As the digital world evolves, so too do the tactics and strategies employed by ransomware attackers. The future of ransomware is poised to become increasingly sophisticated, leveraging emerging technologies and exploiting vulnerabilities in both hardware and software. Analysts predict a rise in targeted ransomware attacks, where cybercriminals will focus on high-value organizations or critical infrastructure, seeking larger payouts. This trend is fueled by the increasing interconnectivity of systems, creating more entry points for attackers. Additionally, we can expect the exploitation of artificial intelligence (AI) to automate and optimize attacks, making them faster and harder to detect.
Advancements in cybersecurity technologies are set to revolutionize how organizations defend against ransomware. The integration of AI and machine learning in cybersecurity solutions will enhance threat detection capabilities, allowing for the identification of unusual patterns that may indicate a potential attack. Organizations are already investing in next-generation endpoint protection, which combines traditional antivirus with advanced threat detection mechanisms. Moreover, the use of automated response systems can significantly reduce the time it takes to contain a breach. Implementing zero-trust architectures, which assume that every attempt to access systems is a potential threat, is also gaining traction. Additionally, advancements in encryption technologies will safeguard data against unauthorized access, mitigating the potential damage from ransomware attacks.
The potential for collaboration between businesses and governments plays a crucial role in combating ransomware threats. Organizations and government agencies are increasingly recognizing that a united front is essential for effective cybersecurity. Joint initiatives can facilitate information sharing about threats and vulnerabilities, providing a broader understanding of the ransomware landscape. For instance, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) has been actively engaging with private sector partners to enhance collective defense measures. Public-private partnerships can also foster the development of common security standards, thereby improving overall resilience against attacks. The establishment of cybersecurity task forces can further enhance collaboration and provide a platform for sharing best practices and incident response strategies.
The future of cybersecurity relies on collective action, continuous innovation, and a proactive approach to address the evolving landscape of ransomware threats.
Final Thoughts
As we conclude our exploration of ransomware, it is clear that proactive measures and informed strategies are essential in the fight against this cyber menace. The financial, emotional, and operational toll it inflicts on victims underscores the urgency for individuals and organizations to adopt effective prevention tactics and recovery plans. Moving forward, a collaborative approach involving technology advancements and regulatory frameworks will be vital in mitigating the risks associated with ransomware, ensuring a safer digital environment for all.
Essential Questionnaire
What is ransomware?
Ransomware is a type of malicious software that encrypts files on a victim’s computer, rendering them inaccessible until a ransom is paid to the attacker.
How do ransomware attacks usually start?
Most ransomware attacks begin through phishing emails, malicious downloads, or exploiting vulnerabilities in software and systems.
Can paying the ransom guarantee recovery of files?
Paying the ransom does not guarantee that you will regain access to your files, as attackers may not provide the decryption keys or could demand additional payments.
What are the legal implications of paying a ransom?
Paying a ransom can have legal consequences, including potential violations of laws regarding funding terrorism or other illicit activities, depending on the jurisdiction.
How can individuals and businesses protect themselves from ransomware?
Effective measures include regular data backups, updating software, employing strong cybersecurity practices, and conducting employee training on recognizing threats.
What should I do if I become a victim of ransomware?
If infected, disconnect from the network, report the incident to authorities, and consult cybersecurity professionals for assistance in recovery.