As Protocol takes center stage, this opening passage beckons readers into a world crafted with good knowledge, ensuring a reading experience that is both absorbing and distinctly original.
Protocols serve as the backbone of communication systems, enabling devices to interact and share information seamlessly. They define the rules and standards governing data exchange, ensuring consistency and reliability across various platforms. Standardization is essential in protocol development, allowing for interoperability among different technologies. In various industries, from telecommunications to healthcare, common communication protocols like TCP/IP and HTTP play pivotal roles, facilitating efficient data transmission and enhancing user experiences.
Understanding the Fundamental Role of Protocols in Communication Systems
Protocols are the backbone of any communication system, orchestrating how data is transmitted and received across various devices. They establish the rules and conventions for communication, ensuring that information can be exchanged accurately and efficiently. Without protocols, devices would struggle to understand one another, leading to confusion and miscommunication. In essence, protocols dictate everything from data formats and transmission speeds to error handling and security measures, making them indispensable in both personal and professional contexts.
Protocols facilitate communication between devices by providing a standardized set of rules that must be followed. This standardization enables interoperability between different systems, allowing devices from various manufacturers to communicate seamlessly. For instance, when you send an email, several protocols work in tandem: SMTP (Simple Mail Transfer Protocol) for sending the email, IMAP (Internet Message Access Protocol) or POP3 (Post Office Protocol) for receiving it, and MIME (Multipurpose Internet Mail Extensions) for handling different types of file attachments. Each protocol serves a specific purpose but must operate in unison to ensure successful communication.
Significance of Standardization in Protocol Development
The significance of standardization in protocol development cannot be overstated. Standardization ensures that devices, applications, and systems can communicate effectively, regardless of their manufacturers. This harmonization reduces compatibility issues and enables users to connect diverse devices without needing proprietary solutions.
Key examples of common communication protocols used in various industries include:
- HTTP/HTTPS: Fundamental for web communication, enabling browsers and servers to exchange information securely.
- FTP (File Transfer Protocol): Used for transferring files between computers over a network, common in web hosting and data sharing.
- Bluetooth: Enables short-range wireless communication between devices, widely used in personal devices like smartphones, headphones, and smartwatches.
- MQTT (Message Queuing Telemetry Transport): A lightweight messaging protocol ideal for IoT (Internet of Things) devices, facilitating efficient communication in constrained environments.
Protocols like these illustrate how standardized frameworks foster reliability and efficiency in communication across various sectors, from telecommunications to healthcare, ensuring that systems can operate cohesively in an increasingly interconnected world.
Analyzing Different Types of Protocols and Their Applications
Protocols are essential frameworks that govern the exchange of data across networks, ensuring communication is effective and reliable. They are categorized based on their functionality and the layer of the network architecture they operate on. Understanding these categories—application, transport, and network protocols—provides insight into their unique roles and applications in real-world scenarios.
Application Protocols
Application protocols operate at the highest layer of the OSI model and are used by applications to communicate over a network. These protocols define the rules for data exchange between end-user services or applications. They play a pivotal role in how users interact with web applications, email services, and file transfers.
Examples of notable application protocols include:
- HTTP (Hypertext Transfer Protocol): This protocol is the foundational technology for data communication on the World Wide Web. It specifies how messages are formatted and transmitted, ensuring that web browsers can retrieve web pages from servers.
- FTP (File Transfer Protocol): This protocol is utilized for transferring files between computer systems on a network. It allows users to upload or download files to and from a server smoothly.
- SMTP (Simple Mail Transfer Protocol): SMTP is the standard protocol for sending emails across the Internet. It defines how email messages are transmitted from a sender’s device to a recipient’s mailbox.
Application protocols are extensively used in various scenarios, such as browsing websites, sharing files, and sending emails, forming the backbone of internet-based communication.
Transport Protocols
Transport protocols are responsible for ensuring the reliable transmission of data between devices. They function at a layer that provides host-to-host communication services for applications, managing the flow of data and error recovery.
Key examples of transport protocols include:
- TCP (Transmission Control Protocol): TCP is a connection-oriented protocol that ensures reliable delivery of data packets through acknowledgment systems. It is widely used in applications requiring high reliability, such as web browsing and email.
- UDP (User Datagram Protocol): Unlike TCP, UDP is a connectionless protocol that sends messages without ensuring their delivery. It’s used in applications that prioritize speed over reliability, such as video streaming and online gaming.
Transport protocols are vital in scenarios where data integrity and speed are essential, influencing how applications perform under various network conditions.
Network Protocols
Network protocols operate at the network layer and are responsible for routing packets across different networks. They define how data packets are addressed, transmitted, and received, ensuring that they reach their intended destination.
Prominent examples of network protocols include:
- IP (Internet Protocol): IP is the protocol responsible for addressing and routing packets of data between devices across networks. It establishes a unique address for every device, facilitating communication over the Internet.
- ICMP (Internet Control Message Protocol): ICMP is used for diagnostic functions and error reporting in networks. It helps manage network conditions by sending messages about packet delivery issues.
These protocols are crucial in real-world applications such as routing data through the Internet, enabling communication between different network segments, and providing feedback on network health.
Understanding the various types of protocols is key to grasping how data moves across networks, ensuring the reliability and efficiency of communications.
Exploring the Evolution of Protocols in Technology
The evolution of protocols in technology marks a significant journey from the early days of computing to the sophisticated standards we utilize today. Understanding this progression helps us appreciate the crucial role protocols play in ensuring seamless communication between systems and devices in our interconnected world.
The historical development of protocols can be traced back to the early days of computing, where basic communication methods were employed to connect simple machines. As technology advanced, so too did the need for more complex and reliable methods of communication. The introduction of standardized protocols, such as TCP/IP in the late 1970s, revolutionized the way devices communicate over networks. This foundational protocol suite laid the groundwork for the modern internet, allowing diverse systems to share data efficiently and reliably.
Technological Advancements Influencing Protocol Design
The design and implementation of protocols have been significantly influenced by various technological advancements. These advancements have not only shaped the protocols themselves but also enhanced user experience and system performance. Below are key technological factors that have played a critical role in this evolution:
- Increased Bandwidth: The growth of bandwidth has allowed protocols to be designed with higher throughput in mind, enabling faster data transmission and richer user experiences.
- Wireless Communication: The shift to wireless technologies has prompted the development of protocols like Wi-Fi and Bluetooth, which facilitate easy and efficient connections between devices without physical cables.
- Cloud Computing: The rise of cloud services has necessitated new protocols, such as REST and GraphQL, which optimize data access and manipulation across distributed systems.
- Security Enhancements: As cybersecurity threats evolved, protocols such as HTTPS and TLS were developed to ensure secure data transmission, protecting user data and privacy.
- Internet of Things (IoT): The proliferation of IoT devices has led to the creation of lightweight protocols like MQTT and CoAP, which enable efficient communication in resource-constrained environments.
The impact of evolving protocols on user experience and system performance is profound. As protocols have become more sophisticated, they have enabled seamless streaming of high-definition content, real-time communication platforms, and efficient data synchronization across devices. For instance, the evolution of HTTP/2 has significantly improved the loading speed of websites by allowing multiple streams of data to be sent simultaneously.
“The development of new protocols not only enhances performance but also shapes the way users interact with technology on a daily basis.”
Protocols continue to adapt as technology advances, ensuring that our digital communication remains efficient and secure. This ongoing evolution is essential for keeping pace with the increasing demand for connectivity and the diverse needs of users across various platforms.
Investigating Security Protocols and Their Importance
The significance of security protocols in today’s digital landscape cannot be overstated. They serve as the backbone of secure communications over networks, ensuring that data remains confidential, intact, and authentic. With the rise of cyber threats, understanding these protocols and their functions is essential for safeguarding sensitive information during transmission.
Security protocols function as established standards that dictate how data is transmitted securely across networks. They encompass a variety of methodologies and systems designed to protect data integrity, confidentiality, and authenticity. Key protocols in this domain include Secure Sockets Layer (SSL), Transport Layer Security (TLS), Internet Protocol Security (IPsec), and Hypertext Transfer Protocol Secure (HTTPS). Each of these protocols plays a critical role in ensuring secure data exchange over the internet.
Security Protocols and Their Roles
A range of security protocols exists, each with a specific purpose in protecting data during transmission. These protocols ensure that the information being transmitted is secure from interception or tampering. The following list highlights several important security protocols and their roles:
- SSL/TLS: These protocols ensure secure communications over networks, establishing an encrypted link between a web server and a browser. This provides confidentiality and integrity for the data exchanged.
- IPsec: Used primarily for securing Internet Protocol (IP) communications, IPsec encrypts and authenticates each IP packet in a communication session, providing a secure tunnel for data transmission.
- HTTPS: An extension of HTTP, HTTPS ensures that communications between a client and server are encrypted using TLS, protecting the integrity and confidentiality of data in transit.
- SFTP: Secure File Transfer Protocol (SFTP) provides a secure method for transferring files over a secure channel, ensuring that the data being transferred is not accessible to unauthorized users.
The relationship between encryption methods and security protocols is foundational. Encryption is the process of converting data into a coded format that can only be read or processed by authorized parties. Security protocols utilize various encryption techniques to safeguard data in transit. For example, SSL/TLS protocols rely on symmetric and asymmetric encryption methods to secure and authenticate data transmissions.
“Encryption transforms data into a secure format, while security protocols establish the guidelines and processes for this secure transmission.”
Real-World Instances of Security Protocols in Action
Security protocols have been pivotal in real-world scenarios, preventing potential data breaches and securing sensitive information. One notable case was the 2013 Target data breach, which compromised the credit and debit card information of millions of customers. Following this incident, the retailer implemented enhanced security measures, including upgraded encryption protocols to protect customer data during transactions.
Similarly, the 2017 Equifax breach, which exposed the personal information of approximately 147 million people, highlighted the importance of robust security protocols. In response, organizations began to prioritize encryption and secure data transmission protocols to mitigate risks associated with identity theft and unauthorized access.
The implementation of proper security protocols not only prevents breaches but also helps organizations maintain customer trust and comply with regulatory standards such as the General Data Protection Regulation (GDPR) and the Health Insurance Portability and Accountability Act (HIPAA). These regulations emphasize the necessity of protecting sensitive data through established security measures, including the use of effective encryption and secure communication protocols.
Designing Efficient Protocols for Future Technologies
The rapid evolution of technology, particularly in areas such as the Internet of Things (IoT) and 5G networks, necessitates the development of efficient communication protocols. These protocols must not only support the growing volume of connected devices and the high-speed demands of new applications but also ensure robust security and reliability. As we design protocols for these emerging technologies, several essential considerations must be taken into account to ensure their effectiveness and adaptability.
Essential Considerations in Protocol Design
Designing protocols for future technologies requires a thorough understanding of various factors that influence performance and usability. Here are key considerations:
- Scalability: Protocols must be able to handle an increasing number of devices without significant degradation in performance. For example, protocols like MQTT (Message Queuing Telemetry Transport) are designed for lightweight messaging and can efficiently scale to thousands of IoT nodes.
- Latency: Low-latency communication is crucial, especially for applications such as autonomous vehicles and real-time monitoring systems. Protocols like QUIC (Quick User Datagram Protocol) are designed to minimize latency compared to traditional TCP.
- Energy Efficiency: Many IoT devices are battery-operated, making energy-efficient protocols essential. Protocols that allow devices to sleep and wake up only when necessary, such as CoAP (Constrained Application Protocol), enhance battery life.
- Interoperability: Future protocols should support seamless interaction between diverse devices and networks. This is exemplified in the development of the Open Connectivity Foundation (OCF), which promotes standards for device interoperability.
- Security: With the increase in connected devices, security protocols must be robust to protect against potential vulnerabilities. Protocols like DTLS (Datagram Transport Layer Security) provide end-to-end security for data transmission.
Innovative Protocol Examples
Numerous innovative protocols are being developed to address the specific needs of future applications. These protocols not only serve current standards but also pave the way for advancements in technology.
- IPv6: The adoption of IPv6 is crucial for accommodating the vast number of devices anticipated in the IoT landscape. Its expanded address space allows for a virtually limitless number of unique IP addresses.
- 5G NR (New Radio): This protocol offers enhanced mobile broadband, low-latency communication, and massive device connectivity, enabling applications such as smart cities and advanced industrial automation.
- LPWAN (Low Power Wide Area Network): Protocols like LoRaWAN are specifically designed for long-range transmissions with low power requirements, making them ideal for IoT applications in remote areas.
- NFC (Near Field Communication): NFC is increasingly being used in applications such as mobile payments and secure access, enabling quick data exchange over short distances.
Challenges and Solutions in Protocol Design
As the demand for efficient communication protocols grows, several challenges arise that need addressing.
- Network Congestion: With increasing device connectivity, network congestion becomes a critical issue. Solutions such as load balancing and the use of edge computing can help distribute network traffic more effectively.
- Security Threats: The proliferation of devices increases the attack surface for cyber threats. Implementing strong encryption methods and regular security updates can mitigate risks associated with vulnerabilities.
- Data Privacy Concerns: As more data is collected from users, privacy concerns must be addressed. Protocols that include built-in privacy features, such as anonymization and user consent, can help safeguard personal information.
- Integration Complexity: Integrating new protocols with existing systems can be challenging. Developing adaptable and backward-compatible protocols can ease the transition while maintaining functionality.
Comparing Proprietary vs. Open Protocols in Industry Practices
In the rapidly evolving landscape of technology, the choice between proprietary and open protocols significantly influences operational efficiency, innovation, and interoperability across various industries. Understanding these protocols is essential for organizations looking to leverage technology to its fullest potential.
Proprietary protocols are developed and controlled by a single entity, granting that entity exclusive rights over the use and implementation of the protocol. In contrast, open protocols are publicly available and can be used, modified, and distributed by anyone. This fundamental difference shapes the operational dynamics and strategic decisions across industries such as telecommunications, information technology, and manufacturing.
Advantages and Disadvantages of Proprietary Protocols
Proprietary protocols offer a distinct set of advantages and disadvantages that can influence their adoption in specific applications.
The primary benefits include:
- Control and Security: Companies can enforce strict security measures, reducing vulnerabilities and ensuring data integrity.
- Custom Features: Tailored functionalities specific to organizational needs can enhance performance and compatibility with existing systems.
- Support and Updates: Dedicated vendor support often leads to timely updates and robust troubleshooting resources.
However, there are notable drawbacks:
- Vendor Lock-in: Organizations may find themselves tied to a specific vendor, limiting flexibility and increasing costs over time.
- Limited Interoperability: Proprietary systems may struggle to integrate with third-party solutions, hindering collaboration and data exchange.
- High Costs: Licensing fees and maintenance costs associated with proprietary protocols can be prohibitive for some companies.
Advantages and Disadvantages of Open Protocols
Open protocols present their own unique set of benefits and challenges that can impact their implementation in various sectors.
Among the advantages are:
- Interoperability: Open protocols are designed to facilitate seamless integration across different platforms and devices, promoting collaboration.
- Cost-Effectiveness: With no licensing fees, organizations can often reduce their overall expenditure on infrastructure and maintenance.
- Community Support: A broad community of developers often contributes to continuous improvements, leading to more innovative solutions.
Conversely, the disadvantages include:
- Security Risks: The open nature can expose vulnerabilities, making systems susceptible to attacks if not properly managed.
- Inconsistent Support: Organizations may face challenges in finding dedicated support, relying instead on community forums which may not be timely or comprehensive.
- Implementation Challenges: Customization can require significant effort and expertise, leading to potential delays in deployment.
Case Studies of Protocol Impact
Analyzing real-world applications of proprietary and open protocols can provide insight into their operational impacts.
A notable case is the telecommunications industry, where proprietary protocols like Signaling System 7 (SS7) dominate due to their security and efficiency in managing voice and data communication. However, the rise of open protocols like SIP (Session Initiation Protocol) has enabled greater interoperability among different service providers, allowing for competitive pricing and innovation.
In the realm of IoT (Internet of Things), many companies, including Amazon and Google, have adopted open protocols such as MQTT (Message Queuing Telemetry Transport) to ensure better device communication and integration. This has led to broader adoption and enhanced user experiences.
The choice between proprietary and open protocols ultimately depends on an organization’s specific needs, market dynamics, and long-term strategic goals. Understanding the implications of each approach can guide businesses in making informed decisions that align with their operational objectives.
Organizing a Protocol Compliance Framework for Organizations
Establishing a robust protocol compliance framework is essential for organizations aiming to maintain operational integrity and regulatory adherence. This framework serves as the backbone of organizational protocols, ensuring that all members understand their responsibilities and the standards expected of them. By implementing a structured approach, organizations can mitigate risks, enhance performance, and foster a culture of compliance.
One of the first steps in organizing a compliance framework is to conduct a comprehensive assessment of all existing protocols. This involves identifying relevant regulations, industry standards, and internal policies that must be adhered to. Once the protocols have been cataloged, organizations should develop clear guidelines outlining the expectations for compliance. These guidelines ensure that everyone is on the same page regarding what constitutes adherence to the various protocols.
Steps to Ensure Compliance with Relevant Protocols
To create an effective compliance framework, organizations should follow these essential steps:
- Conduct a compliance audit to identify existing protocols and gaps in adherence.
- Establish a clear set of compliance guidelines, ensuring they are accessible to all team members.
- Implement training programs to educate staff on compliance expectations and procedures.
- Designate compliance officers or teams responsible for overseeing adherence to protocols.
- Utilize technology solutions to track compliance metrics and streamline reporting.
These steps help form a comprehensive roadmap that ensures every member of the organization is equipped to comply with relevant protocols effectively.
Methods to Monitor and Enforce Protocol Adherence
Monitoring and enforcing adherence to protocols is crucial for maintaining a culture of compliance. Organizations can employ various methods to ensure that these protocols are being followed:
- Regular compliance audits and assessments to evaluate adherence and identify areas for improvement.
- Creating a feedback loop where employees can report non-compliance without fear of retribution.
- Implementing performance metrics that include compliance as a key performance indicator.
- Conducting regular training and refreshers to keep compliance top-of-mind for all staff.
- Leveraging technology such as compliance management software to automate tracking and reporting.
These methods not only facilitate adherence but also encourage a proactive approach among staff to maintain compliance.
Impact of Compliance on Organizational Effectiveness
Adhering to established protocols has a significant impact on the overall effectiveness of an organization. Compliance not only reduces the risk of legal penalties but also enhances operational efficiency and builds stakeholder trust. Here are some key ways compliance influences organizational effectiveness:
- Improved risk management, leading to fewer incidents and disruptions in operations.
- Enhanced reputation, fostering trust with clients, partners, and regulatory bodies.
- Increased employee morale, as a clear understanding of protocols promotes a sense of stability and security.
- Streamlined processes, as compliance often leads to the identification of inefficiencies and areas for improvement.
- Better financial performance, as non-compliance can lead to costly fines and penalties.
By recognizing the importance of compliance, organizations can align their operational goals with regulatory requirements, ultimately leading to greater success and sustainability.
Creating a Comprehensive Documentation for Protocol Usage
Creating comprehensive documentation for protocol usage is essential for ensuring that all stakeholders understand how to effectively implement and utilize the protocol. Clear documentation helps streamline operations, enhances communication, and minimizes the risk of errors during protocol execution.
Key elements should be included in protocol documentation to ensure it serves its purpose effectively. These elements enhance user comprehension and facilitate successful protocol implementation across various teams.
Essential Elements of Protocol Documentation
Effective protocol documentation should include a variety of critical components to provide clarity and facilitate usability. These elements ensure that users can easily navigate through the documentation and apply the protocol effectively:
- Overview of the Protocol: A succinct summary that describes the purpose and scope of the protocol, including expected outcomes and key stakeholders involved.
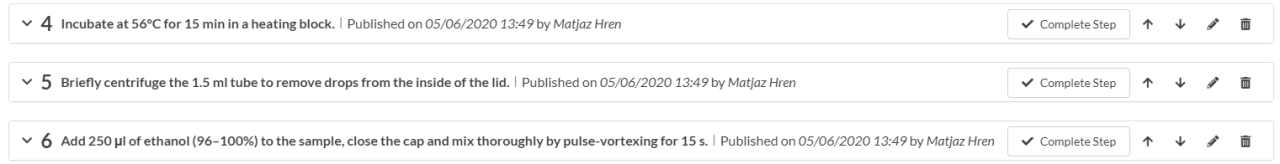
- Step-by-Step Instructions: Detailed, sequential instructions that Artikel how to execute the protocol. This section should include any necessary prerequisites or setup steps.
- Definitions and Terminology: A glossary that defines any technical terms or acronyms used within the documentation to avoid confusion.
- Roles and Responsibilities: Clearly defined roles for individuals involved in the protocol, including responsibilities and expectations for each role.
- Examples and Case Studies: Real-life scenarios or case studies that demonstrate the application of the protocol, providing users with relatable contexts.
- Visual Aids: Diagrams, flowcharts, or screenshots that illustrate complex processes or steps within the protocol, aiding visual learners.
- FAQs and Troubleshooting: A section that addresses common questions and issues users may encounter, along with solutions to facilitate smoother implementation.
- References and Resources: A list of additional resources, such as relevant literature or external tools, for users seeking further information.
The significance of clear documentation cannot be overstated. It serves as a critical resource that enhances understanding and facilitates the practical application of protocols. When documentation is well-structured and easy to follow, it reduces the likelihood of misunderstandings and errors, ultimately leading to more successful outcomes.
Effective Documentation Practices
Leading organizations adopt specific practices that ensure their protocol documentation is both effective and user-friendly. These practices contribute to consistent usage and foster a culture of clarity and collaboration.
- Version Control: Implementing version control systems to keep track of changes made to the documentation ensures that users always refer to the most current information. This practice prevents misinformation from spreading due to outdated materials.
- User-Centric Design: A focus on the end-user experience by utilizing plain language, intuitive layouts, and accessible formats enhances usability. This practice includes testing documentation with actual users to gather feedback and make necessary improvements.
- Regular Updates and Reviews: Establishing a routine for reviewing and updating documentation keeps it relevant and accurate. This process can involve periodic audits and soliciting input from users to identify areas for enhancement.
- Cross-Functional Collaboration: Encouraging collaboration between different teams during the documentation process ensures that diverse perspectives are considered, leading to more comprehensive and effective content.
Organizations like Google and Microsoft exemplify effective documentation practices by integrating user feedback into their documentation processes, maintaining clear version control, and offering extensive training materials that support users in understanding complex protocols. Such practices not only streamline adoption but also enhance overall efficiency and effectiveness in protocol implementation.
Closure
In conclusion, understanding protocols and their significance sheds light on how modern communication systems operate. As technology evolves, so too will the protocols that underpin our interactions, making it crucial for industries and organizations to stay informed and adaptable. By investing in efficient protocol designs and ensuring compliance, businesses can leverage the full potential of these systems, leading to improved performance and security.
FAQs
What is a protocol in communication?
A protocol is a set of rules governing data communication between devices, ensuring proper data exchange and interaction.
Why is standardization important in protocols?
Standardization ensures interoperability among different systems and devices, allowing them to communicate effectively and reliably.
What are some examples of common communication protocols?
Examples include TCP/IP for internet communication, HTTP for web browsing, and SMTP for email transmission.
How have protocols evolved over time?
Protocols have evolved from early computing standards to sophisticated systems that accommodate modern technologies like IoT and 5G.
What role do security protocols play?
Security protocols safeguard data transmission by implementing encryption and authentication measures, protecting against breaches.
What challenges arise in designing new protocols?
Challenges include ensuring compatibility with existing technologies, maintaining security, and accommodating future advancements.