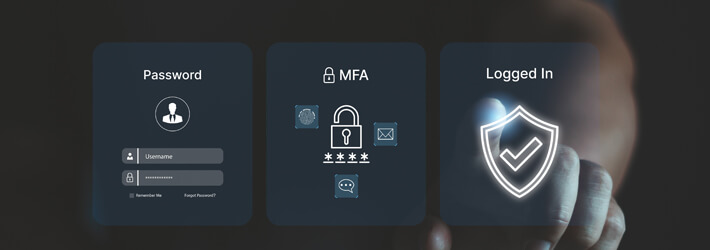
Multi-factor Authentication (MFA) is revolutionizing the way we secure our online accounts, creating layers of protection that go beyond the traditional username and password. Imagine a world where your digital identity is safeguarded by multiple defenses, significantly reducing the risk of unauthorized access. As cyber threats become increasingly sophisticated, the importance of MFA cannot be overstated. It serves as a crucial barrier against data breaches, ensuring that even if one method of verification is compromised, an intruder cannot access sensitive information without additional credentials.
This innovative approach leverages various authentication methods, such as SMS codes, biometrics, and authentication apps, each enhancing security and user confidence. By understanding MFA’s role in thwarting cybercriminals, we can appreciate its necessity in our daily digital interactions. It’s not just a security measure; it’s a proactive strategy that empowers users to take control of their online safety.
Multi-factor Authentication
Multi-factor Authentication (MFA) is a security mechanism that requires users to provide two or more verification factors to gain access to online accounts, systems, or applications. This is an essential layer of security that adds an extra barrier against unauthorized access, significantly reducing the likelihood of cyberattacks. With the increasing number of data breaches and cyber threats, implementing MFA has become not just a best practice, but a necessity for both individuals and organizations. By utilizing multiple factors—something you know (like a password), something you have (like a smartphone or hardware token), and something you are (like a fingerprint or facial recognition)—MFA helps to ensure that even if one factor is compromised, unauthorized access can still be prevented.
Relationship Between MFA and Data Breaches
The relationship between Multi-factor Authentication and data breaches is crucial in understanding the landscape of cybersecurity. By employing MFA, organizations can significantly mitigate the risk of data breaches. Numerous high-profile incidents have demonstrated the vulnerabilities associated with relying solely on passwords. For instance:
1. Yahoo Data Breach (2013-2014): Over 3 billion accounts were compromised in a series of breaches. If MFA had been in place, it could have rendered stolen credentials useless, as attackers would still need the second factor to access accounts.
2. Target Data Breach (2013): Hackers gained access to 40 million credit and debit card accounts. Implementing MFA for internal systems might have prevented the attackers from moving laterally within the network after initial access.
3. Twitter Breach (2020): High-profile accounts were compromised, leading to scams and misinformation. Stronger authentication methods like MFA could have secured these accounts against unauthorized access, highlighting the importance of multiple verification methods.
These examples illustrate how implementing MFA could have changed the outcomes of these breaches, emphasizing its importance in modern cybersecurity strategies.
General Principles Behind MFA
The general principles behind Multi-factor Authentication revolve around enhancing security through layered verification. This approach is predicated on a few key concepts:
– Layered Security: By requiring multiple forms of identification, MFA creates layers of security that make it much harder for unauthorized individuals to gain access. Each additional factor increases the difficulty for potential attackers.
– User Awareness: MFA initiatives also promote user awareness regarding the importance of secure practices. It encourages users to be more vigilant about their online security, especially regarding suspicious activities or requests for personal information.
– Adaptive Authentication: Some MFA systems can adapt their requirements based on risk assessment. For example, if a login attempt is made from an unusual location, additional verification may be triggered, further ensuring security.
These principles highlight the transformative role MFA plays in enhancing user security, ultimately leading to a more robust defense against cyber threats.
Different Types of Multi-factor Authentication Methods
Multi-factor Authentication (MFA) enhances security by requiring users to provide multiple forms of verification before gaining access to an account or system. This layered approach safeguards sensitive information against unauthorized access. With the rise in cyber threats, understanding the various methods available for MFA is crucial for individuals and organizations seeking to bolster their security measures. Below, we delve into four distinct methods of MFA, exploring their mechanisms, advantages, and disadvantages.
SMS and Voice Call Verification
SMS and voice call verification is one of the most common methods of MFA. In this approach, users receive a one-time code via text message or a phone call after entering their password. This code must be input into the login interface to gain access.
The primary advantage of SMS and voice call verification is its convenience. Most users have mobile phones that can receive messages or calls, making it easy to implement. Furthermore, this method is generally user-friendly, requiring minimal technical knowledge.
However, there are notable disadvantages. SMS messages can be intercepted through techniques like SIM swapping or man-in-the-middle attacks, potentially leading to unauthorized access. Additionally, users in areas with poor cellular service may face delays or failure in receiving messages. This lack of reliability can hinder access to important accounts or services.
Authenticator Apps
Authenticator apps generate time-based one-time passwords (TOTPs) that users must enter alongside their passwords to log in. These apps, such as Google Authenticator or Authy, generate codes that refresh every 30 seconds.
The effectiveness of authenticator apps lies in their independence from cellular networks. Users do not need to rely on SMS delivery, reducing the risk of interception. Furthermore, these apps provide a more secure environment since the codes are generated locally on the device.
On the downside, if a user loses access to their device or the app is uninstalled, recovering access can become difficult. It often requires backup codes or additional support from service providers, leading to potential frustration. Additionally, not all services support authenticator apps, which limits their applicability.
Hardware Tokens
Hardware tokens are physical devices that generate a one-time password or have a display to confirm a login action. Users must possess the token during the login process, ensuring a heightened level of security.
The primary advantage of hardware tokens is their strong security. Unlike SMS or apps that may be vulnerable to interception, hardware tokens do not rely on internet or cellular connectivity, making them less susceptible to hacking. They are especially useful in high-security environments, such as banks or government agencies, where safeguarding sensitive information is paramount.
However, the drawbacks include cost and portability. Organizations must purchase tokens for each user, which can become expensive. Furthermore, users may forget or misplace their tokens, leading to access issues. This added layer of hardware can also be cumbersome, especially for users who prefer a more streamlined experience.
Biometric Authentication
Biometric authentication uses unique biological traits, such as fingerprints, facial recognition, or iris scans, to verify a user’s identity. This method is becoming increasingly popular due to the advancement of biometric technology in smartphones and other devices.
The main advantage of biometric authentication is its user-friendliness. Users can quickly unlock accounts or devices through simple gestures, like placing a finger on a scanner or looking at a camera. This convenience encourages adoption and enhances user experience, as there is no need to remember additional passwords or codes.
On the contrary, biometric authentication raises privacy concerns. Users may be wary about storing their biometric data, fearing misuse or leakage. Additionally, biometric systems can experience false rejections or acceptances, leading to potential access issues. Environmental factors, such as lighting conditions for facial recognition, can also affect performance, indicating that while biometric methods are innovative, they are still evolving.
| Method | Effectiveness | User-Friendliness |
|---|---|---|
| SMS and Voice Call Verification | Moderate | High |
| Authenticator Apps | High | Moderate |
| Hardware Tokens | Very High | Low |
| Biometric Authentication | High | Very High |
The Role of Multi-factor Authentication in Various Industries

Multi-factor Authentication (MFA) has become an essential security measure across various industries, addressing the increasing threats posed by cyberattacks. By requiring multiple forms of verification before granting access to sensitive data, organizations can significantly enhance their security posture. As we delve into the specific applications of MFA in finance, healthcare, and education, we will also examine the unique challenges faced by each sector, alongside relevant case studies demonstrating the effectiveness of MFA.
Implementation of MFA in Finance
The finance sector is one of the most heavily regulated industries, making the implementation of MFA a critical component of their cybersecurity strategy. Financial institutions such as banks and investment firms are prime targets for cybercriminals due to the sensitive nature of their data. MFA in finance typically includes factors such as biometric verification, SMS codes, and security tokens.
Key challenges faced by the finance sector include:
- Inconvenience to customers during authentication processes, which can lead to reduced customer satisfaction.
- Integration with existing legacy systems that may not support modern authentication methods.
- Compliance with regulatory frameworks such as the Payment Card Industry Data Security Standard (PCI DSS) which mandates MFA for certain transactions.
A notable case of successful MFA implementation occurred with a major bank that experienced a significant decrease in account takeover incidents after integrating MFA across all online banking services. This proactive measure reinforced customer trust and secured sensitive financial information.
Implementation of MFA in Healthcare
In the healthcare industry, MFA is crucial due to the sensitive nature of personal health information (PHI). Healthcare organizations must comply with strict regulations such as the Health Insurance Portability and Accountability Act (HIPAA), which necessitates robust security measures. MFA solutions in healthcare often involve a combination of smart cards, pin codes, and biometric authentication.
Challenges specific to the healthcare sector include:
- Balancing ease of access for medical staff with stringent security protocols to protect patient data.
- Implementing MFA without disrupting patient care or workflows in high-pressure environments.
- Educating employees about the importance of MFA and ensuring compliance with security policies.
A compelling case study in healthcare involved a hospital that implemented MFA to safeguard its Electronic Health Record (EHR) systems. Following the integration, the hospital reported a 50% reduction in unauthorized access attempts, significantly enhancing patient confidentiality and trust.
Implementation of MFA in Education
Educational institutions have increasingly adopted MFA to protect sensitive student and staff data from breaches. With the rise of online learning, protecting digital platforms has become paramount. MFA methods in education often include email verification, one-time passwords (OTPs), and device-specific authentication.
Challenges faced by educational institutions include:
- Limited budgets that may restrict the adoption of advanced MFA technologies.
- Resistance from students and faculty who may view additional authentication steps as burdensome.
- Varying levels of digital literacy among staff and students, affecting overall compliance and effectiveness of MFA.
An illustrative case in education showed that a university that implemented MFA for access to its online portals saw a dramatic decline in phishing attacks. By requiring additional authentication, the institution was able to protect its community’s personal information and enhance their overall online security.
Regulatory Influences on MFA Adoption
Regulatory requirements play a significant role in the adoption of MFA across different sectors. Various laws and regulations, such as GDPR in Europe and HIPAA in the United States, include mandates for strong authentication practices to safeguard sensitive data.
The influence of regulations on MFA adoption includes:
- Forcing organizations to implement stricter security measures to comply with legal standards.
- Providing frameworks that guide organizations in establishing robust authentication practices.
- Encouraging companies to prioritize cybersecurity investments to avoid potential fines and legal repercussions.
In conclusion, the role of MFA in finance, healthcare, and education is pivotal in safeguarding sensitive information against cyber threats. By understanding the unique challenges each sector faces and learning from successful implementations, organizations can enhance their security frameworks and comply with evolving regulatory requirements.
Challenges and Limitations of Multi-factor Authentication
Implementing Multi-factor Authentication (MFA) can significantly enhance an organization’s security posture, but it is not without its challenges and limitations. Organizations often face various hurdles during the deployment and ongoing use of MFA solutions. Understanding these challenges is crucial for developing effective security strategies.
Common Challenges in Implementing MFA
Organizations frequently encounter several challenges when implementing MFA systems. These challenges can hinder the effectiveness of MFA and may require careful consideration and planning to address.
- Integration with Existing Systems: Many organizations struggle to integrate MFA with legacy systems and applications. Compatibility issues can arise, causing delays and requiring additional resources for customization.
- Cost of Implementation: The financial investment required for deploying MFA can be substantial. This includes costs for software, hardware, and potential training for staff, which may deter some organizations from adopting MFA.
- Management of Multiple Authentication Methods: Organizations may offer various authentication methods to accommodate user preferences, leading to complexities in managing and securing these multiple options.
User Experience Concerns Related to MFA
User experience plays a critical role in the adoption of MFA solutions. If the user experience is perceived as cumbersome or disruptive, it could lead to lower adoption rates among employees and customers.
- Increased Steps for Access: MFA introduces additional steps to the login process, which may frustrate users accustomed to single-factor authentication. This can lead to resistance or non-compliance.
- Time Consumption: Users may find MFA time-consuming, particularly if they are frequently required to enter codes or use authentication apps, potentially impacting productivity.
- Challenges for Non-Technical Users: Less tech-savvy individuals may struggle with MFA processes, leading to confusion and increased requests for support, which can strain IT resources.
Limitations of Multi-factor Authentication
While MFA significantly improves security, it has inherent limitations that organizations should consider when planning their security architecture.
- Not Foolproof Against All Threats: MFA can mitigate risks but does not eliminate them entirely. For instance, sophisticated attacks such as SIM swapping can bypass MFA systems.
- Dependence on User Behavior: The effectiveness of MFA often relies on users maintaining good security hygiene, such as not sharing authentication codes or using weak passwords, which can compromise the system.
- Potential for Phishing Attacks: Users can still fall victim to phishing attacks even with MFA in place, as attackers can trick users into providing their second-factor credentials.
The implementation of MFA is a step forward in enhancing security, but organizations must remain vigilant and address its limitations and challenges to maximize effectiveness.
Future Trends in Multi-factor Authentication Technologies
As the digital landscape continuously evolves, so does the need for robust security measures like Multi-factor Authentication (MFA). Future trends in MFA are being shaped by emerging technologies such as biometrics and artificial intelligence (AI). Understanding these advancements is crucial for organizations looking to enhance their security protocols against increasingly sophisticated cyber threats.
The integration of biometric authentication, including fingerprint recognition and facial scanning, is becoming more prevalent. These technologies offer unique advantages over traditional methods, as they rely on individual physical traits, making them hard to replicate or steal. AI-driven security measures are also gaining traction, utilizing machine learning algorithms to analyze user behavior patterns and detect anomalies in real-time. Such technologies not only improve the security of MFA but also enhance user experience by streamlining the authentication process.
Technological Advances Influencing MFA
Emerging technologies are expected to play a significant role in shaping the future of MFA. Below is a summary of potential advancements in MFA, along with their expected impact on security protocols:
| Technology | Potential Advancements | Expected Impact on Security |
|---|---|---|
| Biometric Authentication | Integration of facial recognition, fingerprint scanners, and voice recognition. | Increased security through unique user identification, reduced reliance on passwords. |
| AI-Driven Security | Real-time threat detection and response through behavior analysis. | Proactive identification of potential breaches, enhanced user experience. |
| Blockchain Technology | Decentralized identity verification systems. | Improved data security and user privacy while minimizing fraud. |
| Continuous Authentication | Ongoing verification based on user behavior, location, and device. | Enhanced security by preventing unauthorized access throughout a session. |
| Smart Wearables | Use of smart devices for authentication (e.g., smart rings, watches). | Convenient and secure access, with reduced friction for users. |
The rise of cyber threats, including sophisticated phishing schemes and ransomware attacks, is pushing organizations to adopt these advanced MFA technologies. As attackers evolve, so must the tools we use to protect against them. The continuous development of MFA strategies will be crucial in safeguarding sensitive information and ensuring secure access in an increasingly interconnected world.
Best Practices for Implementing Multi-factor Authentication
Multi-factor Authentication (MFA) is a critical component for enhancing security across organizational systems. Implementing MFA effectively requires a structured approach and awareness of potential challenges. Below are comprehensive guidelines for organizations aiming to adopt MFA while avoiding common pitfalls.
Steps for Effective MFA Implementation
Implementing MFA involves several key steps that ensure both security and user convenience. A well-planned strategy can lead to a smoother transition and greater acceptance among users.
- Assess Current Security Needs: Evaluate existing authentication methods and identify weaknesses in your security posture.
- Choose Appropriate Authentication Methods: Select MFA types such as SMS codes, authenticator apps, biometrics, or hardware tokens based on user familiarity and organizational requirements.
- Develop a Rollout Plan: Create a timeline and communication plan that Artikels how MFA will be introduced to users, including training sessions and support resources.
- Pilot the Implementation: Run a pilot program with a small user group to identify any issues before a full-scale rollout.
- Monitor and Adjust: After implementing MFA, continuously monitor its performance and solicit user feedback to make necessary adjustments.
Avoiding Common Pitfalls During MFA Setup
While implementing MFA, organizations must be aware of potential pitfalls that can undermine the effectiveness of the system. By knowing what to avoid, the transition to MFA can be more seamless.
Ensure that the chosen MFA methods are user-friendly to prevent resistance from end-users.
- Neglecting User Experience: Complicated authentication processes can frustrate users, leading to non-compliance.
- Inadequate Training: Failing to educate users about MFA can result in confusion and misuse of the authentication system.
- Overlooking Backup Options: Not providing backup or recovery options for lost authentication devices can lock users out of critical systems.
- Excessive Reliance on One Method: Depending solely on a single MFA method can increase vulnerability; diversify to strengthen security.
- Ignoring Regulatory Requirements: Make sure that MFA implementation complies with industry standards and regulations to avoid potential legal issues.
Importance of User Training and Awareness
User training is central to the successful adoption of MFA within organizations. Without adequate understanding and awareness, even the most robust MFA systems can be compromised.
Effective training empowers users to utilize MFA features confidently and securely.
Training should focus on the following aspects:
- Understanding MFA Mechanisms: Users should be educated about how MFA works and why it is essential for security.
- Recognizing Phishing Attempts: Training should include how to identify phishing attempts that could bypass MFA.
- Acknowledging the Importance of Device Security: Users must understand the need to protect their authentication devices from loss or theft.
- Support and Resources: Provide ongoing help, FAQs, and resources to assist users as they navigate MFA processes.
The Impact of Multi-factor Authentication on User Behavior
The implementation of Multi-factor Authentication (MFA) has significantly transformed user behavior, particularly in terms of security awareness and risk management. As organizations incorporate MFA to bolster security measures, users are becoming increasingly aware of the importance of protecting sensitive information. This heightened awareness often leads to a more proactive approach to personal and organizational security.
MFA not only adds an extra layer of security but also influences users’ perceptions of risk. With the knowledge that unauthorized access is more difficult, users tend to engage differently with online platforms. They often adopt more secure practices and become more vigilant about potential threats. For instance, after the integration of MFA, users are likely to be more inclined to update passwords regularly and to scrutinize the legitimacy of communications that request personal information.
User Engagement Changes Post-MFA Implementation
The shift towards MFA has led to noticeable changes in user engagement and response to security incidents. Users, armed with the understanding that their accounts are more secure, often display a greater willingness to interact with online services. This trend can be summarized through the following observations:
- Increased Adoption of Security Practices: Users have started to adopt additional security measures, such as enabling alerts for account activity and utilizing password managers to maintain complex passwords.
- Enhanced Response to Phishing Attempts: Post-MFA implementation, users display heightened skepticism towards unsolicited emails or messages, often double-checking the source before responding.
- More Engagement with Security Training: Organizations have observed an uptick in user participation in security training programs, as employees recognize the importance of being informed about potential threats.
Psychological Aspects of MFA and Security Perception
The psychological impact of MFA on users extends beyond mere compliance. By requiring multiple forms of verification, MFA fosters a sense of security among users. They often perceive their online activities as more protected, which can lead to increased trust in the platforms they use.
Additionally, the inconvenience sometimes associated with MFA can also lead users to reevaluate their security practices. For example, while the extra steps may initially seem burdensome, they often lead users to appreciate the importance of their data security.
“The feeling of security is paramount in today’s digital landscape, and MFA contributes significantly to that perception.”
Moreover, organizations that implement MFA can cultivate a culture of security awareness, where employees feel empowered to take ownership of their digital safety. This cultural shift not only enhances individual behavior but also strengthens the overall security posture of the organization.
Concluding Remarks
In conclusion, Multi-factor Authentication (MFA) stands as a vital component in the ever-evolving landscape of cybersecurity. Its ability to fortify online accounts against breaches not only protects sensitive data but also cultivates a culture of security awareness among users. As we navigate a future filled with emerging threats and advanced technologies, embracing MFA is not just a choice but a necessity for individuals and organizations alike. By investing in robust authentication measures, we can enhance our digital security and enjoy a safer online experience.
Q&A
What is Multi-factor Authentication (MFA)?
MFA is a security measure that requires users to provide two or more verification factors to gain access to an account, making it harder for unauthorized users to compromise sensitive information.
How does MFA enhance security?
By requiring multiple forms of verification, MFA minimizes the risk of account breaches even if one factor, like a password, is compromised.
Is MFA user-friendly?
While MFA can add an extra step in the login process, many methods like biometrics or authentication apps are designed for convenience, improving overall user experience with better security.
Are there any downsides to using MFA?
Some users may find MFA inconvenient, and organizations may face challenges in implementation and user adoption, but the security benefits generally outweigh the drawbacks.
What industries benefit most from MFA?
Industries such as finance, healthcare, and education benefit significantly from MFA due to the sensitive nature of the data they handle and the regulatory requirements they must comply with.