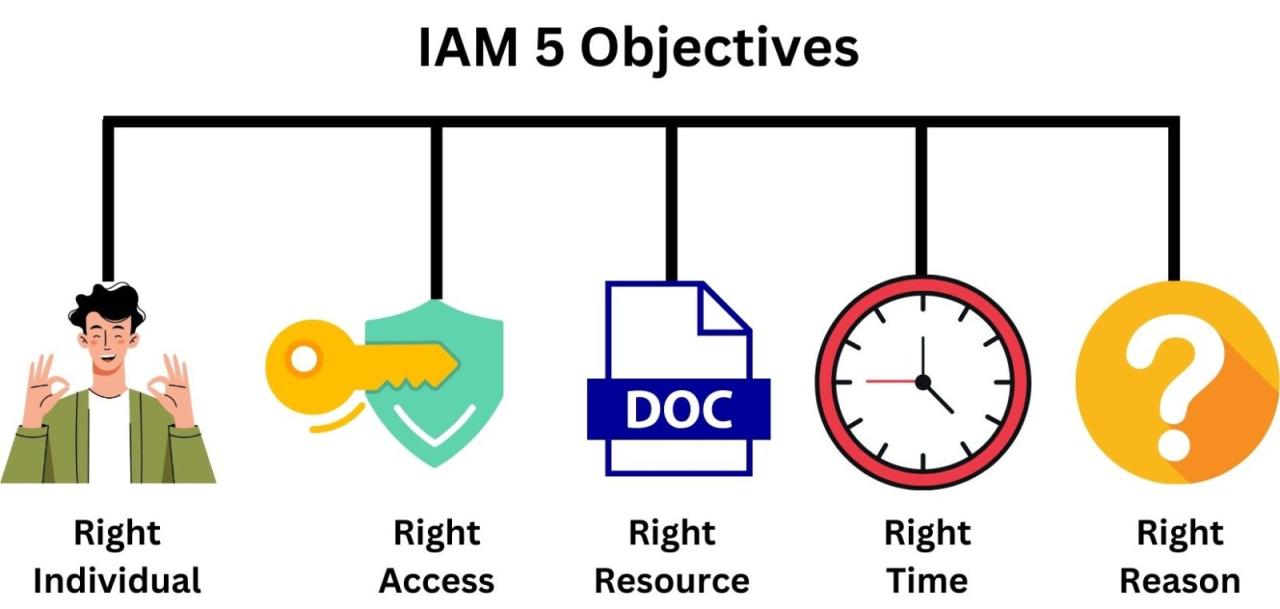
Identity Access Management (IAM) plays a pivotal role in today’s digital landscape, ensuring that the right individuals have the appropriate access to technology resources. With the rise of cyber threats and remote work, understanding IAM has never been more crucial. This comprehensive system encompasses policies, technologies, and practices that manage digital identities, safeguarding sensitive information while streamlining user access.
From organizations adopting robust IAM policies to prevent unauthorized access, to leveraging advanced technologies like multi-factor authentication and encryption, the strategies and tools available create a more secure environment. As businesses increasingly rely on technology, the integration and effectiveness of IAM systems are vital in maintaining a strong cybersecurity posture.
Understanding the Fundamentals of Identity Access Management
Identity Access Management (IAM) is a crucial framework within IT that ensures the right individuals have the appropriate access to technology resources. As organizations evolve and their digital ecosystems grow, the need for robust IAM solutions has become increasingly significant. IAM not only enhances security but also streamlines user experiences and compliance with regulations. By managing identities and controlling access effectively, organizations can safeguard sensitive information and maintain operational integrity.
The core principles of IAM are centered around the concepts of identity assurance, access control, and governance. Identity assurance involves verifying the identities of users through authentication methods, including passwords, biometrics, and multi-factor authentication. Access control refers to the policies and technologies that determine who can access specific resources and under what circumstances. Governance encompasses the processes that ensure compliance with internal policies and external regulations, such as GDPR or HIPAA. These principles work synergistically to build a secure environment where only authorized users have access to critical resources, thereby minimizing the risk of data breaches.
Key Components of IAM Systems
IAM systems comprise several key components that collaborate to protect organizational resources. Understanding these components helps in implementing effective IAM solutions.
1. Authentication: This component verifies the identity of users attempting to access resources. It includes various methods such as single sign-on (SSO), multi-factor authentication (MFA), and social logins, which enhance security by requiring multiple forms of identification.
2. Authorization: Once a user is authenticated, authorization determines what resources they can access. This is typically managed through role-based access control (RBAC) or attribute-based access control (ABAC) policies, which define user roles and permissions based on their attributes.
3. Identity Governance: This involves the policies and processes that manage user identities and ensure compliance. Regularly reviewing and auditing access rights is essential to maintain security and governance.
4. Directory Services: These are centralized databases that store user identities and attributes. They facilitate user management and provide the necessary information for authentication and authorization processes.
5. Audit and Reporting: Continuous monitoring and logging of access events are crucial for identifying potential security threats. IAM systems generate reports that help organizations assess compliance and detect unusual activities.
Implementing IAM policies can significantly enhance security within organizations. Examples include:
– Least Privilege Access: Ensuring users have only the access necessary to perform their jobs, reducing the risk of unauthorized access.
– Regular Access Reviews: Conducting audits on user access rights to ensure compliance and adjust permissions as needed.
– Password Management Policies: Enforcing strong password creation and regular changes to mitigate the risk of account compromises.
– Incident Response Policies: Establishing protocols for quickly responding to security breaches or access violations.
By integrating these components and policies, organizations can create a robust IAM framework that not only protects sensitive data but also promotes operational efficiency.
The Role of IAM in Cybersecurity Strategies
Identity Access Management (IAM) serves as a pivotal component in bolstering an organization’s cybersecurity framework. By ensuring that the right individuals have the appropriate access to technology resources, IAM mitigates the risks associated with data breaches and unauthorized access. In today’s digital landscape, where threats are increasingly sophisticated, implementing a robust IAM strategy is crucial for maintaining data integrity and securing sensitive information.
The effectiveness of any cybersecurity strategy is largely determined by how well it can control user access and authenticate identities. IAM systems facilitate this by providing comprehensive user identity management, including user provisioning, de-provisioning, and access rights management. This not only helps prevent unauthorized access but also allows organizations to enforce compliance with regulatory requirements.
Comparison of IAM Solutions
When analyzing different IAM solutions, it is essential to consider their capabilities in preventing data breaches and managing unauthorized access. Various IAM solutions offer different features, effectiveness levels, and user experiences. The following points highlight key comparisons:
- Cloud-based IAM Solutions: Popular for their scalability, cloud IAM options, such as Okta and Microsoft Azure Active Directory, provide robust security features and easy integration with other cloud services. They are particularly effective for organizations with remote teams, as they facilitate secure access from anywhere.
- On-premises IAM Solutions: Traditional IAM systems like IBM Security Identity Governance provide comprehensive control over organizational data and resources. However, they may require significant investment in hardware and ongoing maintenance, which can be a drawback for some businesses.
- Hybrid IAM Solutions: Combining cloud and on-premises elements, hybrid solutions offer flexibility. They allow organizations to maintain sensitive data on-site while leveraging cloud capabilities for broader access management.
The integration of IAM with other security measures enhances its effectiveness. Multi-Factor Authentication (MFA) adds an extra layer of security by requiring users to provide two or more verification factors. This significantly reduces the risk of unauthorized access, as it is much harder for attackers to compromise multiple authentication methods. Encryption, on the other hand, ensures that even if unauthorized access occurs, the data remains unreadable without the decryption key.
An IAM system that integrates seamlessly with MFA and encryption protocols offers a comprehensive solution to a multitude of security challenges, thereby solidifying its place in an organization’s cybersecurity strategy. In essence, IAM is not just about managing access; it is about establishing a fortified environment where data is protected from the ever-evolving threats in cyberspace.
Challenges and Solutions in Implementing IAM

Implementing Identity Access Management (IAM) systems can be a complex endeavor for organizations, often presenting a variety of challenges. Understanding these challenges and their solutions is crucial for successful implementation and ongoing management of IAM systems.
Common Challenges and Their Solutions
Organizations often face several key challenges during IAM implementation, which can hinder security and operational efficiency. Addressing these issues promptly can lead to a more secure and streamlined IAM process.
One prevalent challenge is *user resistance to new systems*. Employees may be accustomed to legacy systems, making the transition difficult. Engaging staff through comprehensive training and clear communication about the benefits of IAM can alleviate fear and resistance.
Another significant hurdle is *integration with existing systems*. Many organizations have a multitude of legacy applications that may not seamlessly connect with new IAM solutions. A practical approach involves selecting IAM solutions that offer robust APIs and customization options, allowing for smoother integration.
The challenge of *regulatory compliance* can also pose significant difficulties. Different regions may have varying requirements for data protection and privacy. To navigate this, organizations should conduct thorough compliance audits and choose IAM solutions that are adaptable to evolving regulatory landscapes.
Additionally, *scalability issues* can arise as organizations grow. IAM solutions must accommodate an increasing number of users and devices. To mitigate this challenge, businesses should consider cloud-based IAM services, which typically offer scalable solutions that can grow with the organization.
Real-World IAM Failures
IAM failures can lead to severe security incidents, as seen in notable cases like the Equifax breach in 2017. The incident was primarily caused by a failure to implement proper access controls and inadequate patch management, exposing sensitive data of millions. Such failures underline the critical importance of consistent updates and monitoring in IAM systems.
Best Practices for Maintaining IAM Systems
Maintaining and updating IAM systems is vital to protect against evolving security threats. Best practices include regular audits and assessments to evaluate the effectiveness of current IAM measures. Organizations should also implement a policy for continuous updates and patches to address vulnerabilities promptly.
Furthermore, employing multi-factor authentication (MFA) enhances security by adding layers of protection beyond just passwords. Regular training for users about security best practices can foster a culture of security awareness, minimizing risks related to human error.
Lastly, establishing a clear incident response plan ensures that organizations can swiftly address any security breaches, minimizing impact and restoring confidence among users and stakeholders. By focusing on these best practices, organizations can enhance their IAM frameworks to adapt to the ever-changing security landscape.
The Future Trends of Identity Access Management
The landscape of Identity Access Management (IAM) is evolving rapidly, driven by technological advancements and changing work environments. As organizations increasingly rely on digital solutions, the future of IAM will be shaped by innovative technologies, the need for robust security measures, and a heightened focus on user experience. This evolution will address emerging challenges and opportunities in securing identities and managing access.
Emerging Technologies in IAM
Artificial Intelligence (AI) and Machine Learning (ML) are emerging as transformative forces in IAM. Their ability to analyze large datasets and identify patterns enhances threat detection and response capabilities. AI-driven IAM solutions can automate identity verification and access control processes, improving efficiency. For instance, predictive analytics can identify unusual behavior that may signify a security breach, allowing organizations to respond proactively.
The integration of biometric authentication methods, such as facial recognition and fingerprint scanning, is also on the rise. These technologies offer a seamless user experience while enhancing security. As AI and ML continue to evolve, we can expect more sophisticated solutions that not only protect systems but also adapt to user behavior and environmental changes.
Identity Verification in Remote Work Environments
With the shift toward remote work, the importance of identity verification has never been clearer. Organizations must ensure that only authorized users can access sensitive information, regardless of location. IAM systems must adapt by incorporating multi-factor authentication (MFA) and continuous verification methods, ensuring that user identities are verified throughout their sessions.
This shift is exemplified by companies adopting zero trust security models, which assume that threats could originate from both inside and outside the organization. This paradigm emphasizes the need for verification at every access point, highlighting the role of IAM in safeguarding remote work environments.
Predictions for IAM Evolution
Looking ahead, IAM is poised to undergo significant evolution over the next five years. Regulatory changes, such as the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA), will drive organizations to prioritize data privacy and compliance. This emphasis will necessitate enhanced IAM frameworks that integrate privacy by design principles.
Technological advancements will also play a crucial role. The rise of decentralized identity systems, where users control their own identity data, could reshape how identities are managed. Blockchain technology may provide a secure and transparent method for identity verification, reducing the risks associated with centralized databases.
As organizations navigate these changes, IAM will become an integral part of their overall security strategy, ensuring that they adapt to evolving threats while fostering trust and compliance with regulatory demands.
Regulatory Compliance and IAM
In today’s data-driven world, organizations must navigate a complex landscape of regulatory compliance that governs data protection, privacy, and security. Identity Access Management (IAM) plays a pivotal role in helping organizations meet these regulatory requirements, including those set forth by GDPR, HIPAA, CCPA, and more. Effective IAM systems not only enhance security but also ensure that companies are aligned with legal standards, thus avoiding hefty fines and reputational damage resulting from non-compliance.
IAM is crucial for regulatory compliance as it provides the framework to manage user identities, access permissions, and data security protocols. For instance, under the General Data Protection Regulation (GDPR), organizations are mandated to implement appropriate security measures to protect personal data. This includes ensuring that only authorized individuals have access to sensitive information. Similarly, the Health Insurance Portability and Accountability Act (HIPAA) sets specific requirements for safeguarding patient data, where IAM can help enforce role-based access controls and audit trails to demonstrate compliance. The alignment of IAM practices with these regulations minimizes the risk of data breaches and protects against identity theft, both of which have significant legal implications.
Relationship Between IAM Practices and Legal Implications
The intersection of IAM practices and legal standards is critical in today’s digital environment. A data breach or incident of identity theft can lead to severe legal repercussions, including fines, litigation, and damage to an organization’s reputation. Most regulations impose strict penalties for non-compliance, which can be financially devastating. For example, under GDPR, fines can reach up to €20 million or 4% of the annual global revenue, whichever is higher. Thus, the legal implications of failing to protect data with robust IAM measures are profound and far-reaching.
IAM systems that effectively manage who can access what data, when, and under what circumstances are essential for safeguarding organizations against such breaches. They provide the necessary controls and monitoring capabilities to not only prevent unauthorized access but also to demonstrate compliance during audits. Organizations that neglect these systems may find themselves vulnerable to attacks, which data shows are increasing at an alarming rate. A recent report indicated that 63% of organizations experienced a data breach in the last year, highlighting the urgent need for comprehensive IAM strategies.
To align IAM strategies with compliance mandates and mitigate risks, organizations should consider the following guidelines:
- Conduct Regular Risk Assessments: Identify potential vulnerabilities in access controls and data management practices to stay ahead of compliance requirements.
- Implement Role-Based Access Control (RBAC): Limit data access based on job roles and responsibilities to minimize exposure of sensitive information.
- Utilize Multi-Factor Authentication (MFA): Strengthen access security by requiring multiple forms of verification before granting access to systems or data.
- Maintain Detailed Audit Logs: Keep comprehensive records of who accessed what data and when, which is crucial for compliance audits and investigations.
- Provide Employee Training: Regularly educate staff on compliance requirements and the importance of IAM practices to foster a culture of security.
By implementing these strategies, organizations can not only align their IAM practices with regulatory compliance but also establish a robust defense against potential legal implications of data breaches and identity theft.
IAM in Cloud Environments
In today’s digital landscape, transitioning to cloud solutions has become a necessity for many organizations. Identity Access Management (IAM) plays a crucial role in ensuring secure access to these cloud environments. This section delves into the unique considerations, challenges, and strategies for effective IAM in the cloud, alongside a comparison with traditional IAM systems.
Cloud environments present distinct challenges for IAM, primarily due to their dynamic nature. Unlike traditional on-premises systems, where boundaries are well-defined, cloud infrastructures are often more fluid and decentralized. This necessitates a robust approach to managing user identities, roles, and permissions. Some key considerations include:
- Scalability: Cloud environments can scale rapidly, leading to potentially thousands of user accounts that need management.
- Multi-tenancy: Multiple customers can share the same cloud infrastructure, requiring stringent access controls to prevent unauthorized data access.
- Integration: Organizations often use a mix of SaaS and on-prem systems, necessitating seamless integration between various IAM solutions.
- Compliance: Adhering to regulations such as GDPR or HIPAA is critical, as failing to do so can lead to significant penalties.
To address these challenges, organizations can employ strategies such as adopting a Zero Trust model, implementing automated provisioning processes, and utilizing identity federation to streamline access across multiple systems.
Comparison of Traditional IAM and Cloud IAM Solutions
Traditional IAM solutions typically involve physical servers and software installations that manage user identities within an organization’s network. In contrast, cloud IAM solutions offer a more flexible approach by leveraging the cloud’s capabilities. Key differences include:
- Deployment: Traditional IAM requires on-premise infrastructure, while cloud IAM solutions are hosted on the cloud, enabling easier access and management.
- Cost: Cloud IAM often operates on a subscription basis, reducing upfront capital expenditures compared to traditional models.
- Updates: Cloud IAM solutions benefit from regular updates and patches without the need for manual intervention, unlike traditional systems.
- Collaboration: Cloud IAM enhances collaboration across remote teams, a crucial feature in today’s hybrid work environments.
These differences highlight the advantages of adopting cloud IAM solutions to meet the evolving needs of organizations.
Pros and Cons of Different IAM Solutions in Cloud Environments
Evaluating the various IAM solutions available for cloud environments is essential for organizations considering their options. Below is a comparative analysis of the pros and cons:
| IAM Solution | Pros | Cons |
|---|---|---|
| Cloud IAM |
|
|
| On-Prem IAM |
|
|
This table encapsulates the key aspects of different IAM solutions, aiding organizations in making informed decisions based on their unique requirements.
User Experience and IAM
In the realm of Identity Access Management (IAM), striking the right balance between security and user experience is essential. Organizations today face the challenge of protecting sensitive data while ensuring that users can access resources seamlessly. A well-designed IAM system should not only safeguard information but also enhance the overall experience for its users.
Achieving this balance requires a strategic approach that incorporates user-centric design principles alongside robust security measures. Organizations must prioritize simplicity and efficiency in their IAM processes to avoid frustrating users, which could lead to security workarounds or non-compliance. Adopting adaptive authentication techniques can also help tailor the security requirements to the context of the user’s actions, allowing for a smoother experience. By implementing features such as Single Sign-On (SSO), organizations can significantly reduce the number of credentials users must manage, thus minimizing the friction often associated with access security.
Improving User Onboarding Processes
Enhancing the user onboarding process while maintaining strong security protocols is crucial for any IAM strategy. The onboarding experience sets the tone for user interaction with the system and can significantly influence overall satisfaction. To optimize this process, organizations can implement the following techniques:
- Streamlined Registration: Simplifying the registration process with clear instructions and reduced input fields can help users complete onboarding quickly.
- Multi-Factor Authentication (MFA): Implementing MFA that is user-friendly, such as SMS or email verification, ensures security without excessive hassle.
- Interactive Guides: Providing step-by-step tutorials or interactive guides during onboarding can help users understand their roles and how to navigate the system effectively.
- Feedback Mechanisms: Incorporating feedback tools allows users to report issues or suggest improvements, creating a sense of involvement and ownership.
These techniques not only improve user satisfaction but also encourage adherence to security protocols.
Case studies illustrate the success of enhancing user experience through IAM adjustments. A notable example is a global banking institution that implemented SSO across its platforms. This change reduced login times by 70%, resulting in increased user productivity and a noticeable decline in help desk calls related to access issues. Another example is an e-commerce company that adopted biometric authentication for its app. Users reported feeling more secure and found the experience smoother, leading to higher conversion rates. These cases underscore the potential of IAM to positively impact user experience while still maintaining stringent security standards.
Final Review
In summary, Identity Access Management (IAM) is not just a technical requirement but a fundamental aspect of an organization’s security strategy. As we move forward, the evolution of IAM will continue to shape how organizations protect their data and manage user access in an ever-changing technological landscape. By embracing emerging trends and adhering to compliance standards, businesses can ensure a secure future while enhancing user experiences.
FAQ Resource
What is the primary purpose of IAM?
The primary purpose of IAM is to ensure that only authorized individuals can access specific resources while maintaining security and compliance.
How does IAM relate to data privacy?
IAM plays a crucial role in data privacy by controlling access to sensitive information and ensuring that personal data is handled according to regulations.
What are the main components of an IAM system?
The main components include identity governance, access management, authentication, and directory services.
Can IAM systems prevent all cyber threats?
While IAM systems significantly enhance security, they cannot prevent all cyber threats. They are a critical part of a broader cybersecurity strategy.
How often should IAM policies be reviewed?
IAM policies should be reviewed regularly, ideally at least annually or whenever there are significant changes in the organization or regulatory requirements.
What role does user training play in IAM?
User training is essential in IAM as it ensures that employees understand security protocols and the importance of protecting their credentials.