Near Field Communication (NFC) is transforming how we connect and interact with technology in our everyday lives. With a simple […]
Category: Uncategorized
Wi-Fi 6 / Wi-Fi 7
As Wi-Fi 6 / Wi-Fi 7 takes center stage, the evolution of wireless technology promises to redefine how we connect, […]
Wide Area Network (Wan)
Wide Area Network (WAN) serves as the backbone of modern communication, connecting distant networks and enabling seamless data exchange across […]
Tech Startup
Tech Startup journeys are often filled with excitement and challenges, as entrepreneurs navigate the competitive landscape of today’s digital world. […]
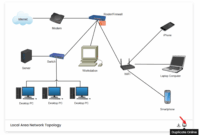
Local Area Network (Lan)
Local Area Network (LAN) serves as the backbone of modern connectivity, facilitating seamless communication and data sharing across various devices […]
Technical Debt
Technical Debt is a crucial concept in software development that can significantly impact the success and longevity of a project. […]
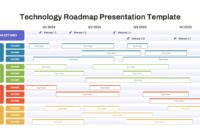
Technology Roadmap
Exploring the realm of Technology Roadmap invites you to discover a vital tool for organizations looking to align their tech […]
Intellectual Property (Ip)
Intellectual Property (IP) serves as the backbone of innovation and creativity in our modern economy, safeguarding the unique ideas and […]
Smart City
Exploring the concept of Smart City reveals a transformative approach to urban living, where technology and data converge to enhance […]
Digital Literacy
Digital Literacy is more than just a buzzword; it’s a vital skill set that empowers individuals to navigate the complexities […]