Zero Trust Architecture is the emerging security framework that flips traditional security models on their heads. Imagine a world where […]
Author: admin
Ethical Hacking Unveiling Opportunities and Impact
Ethical Hacking sets the stage for an enthralling narrative, offering insights into the world where cybersecurity meets innovative problem-solving. As […]
Biometrics Revolutionizing Security Systems and Trust
Biometrics is transforming the way we approach security, merging technology with the unique characteristics of our bodies to create systems […]
Multi-factor Authentication (MFA) Enhancing Security
Multi-factor Authentication (MFA) sets the stage for a deeper understanding of cybersecurity, acting as a gatekeeper that elevates security beyond […]
Malware Unraveled The Intricacies of Cyber Threats
Malware is more than just a buzzword; it’s a pivotal element in the contemporary cyber landscape that affects individuals and […]
Phishing Unraveled Understanding the Threat Landscape
Kicking off with Phishing, this opening paragraph delves into a growing concern that has impacted countless individuals and organizations alike. […]
Ransomware Unraveled Understanding its Impact and Threats
Ransomware has emerged as a formidable adversary in today’s digital landscape, inflicting chaos on both individuals and organizations alike. With […]
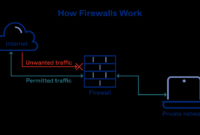
Firewall Essentials for Modern Network Security
Firewall technology serves as a crucial guardian in the realm of network security, standing firm against a myriad of cyber […]
Cybersecurity Understanding Its Importance and Impact
In today’s digital landscape, Cybersecurity emerges as a critical pillar that safeguards information and maintains trust in our interconnected world. […]
Encryption Unveiled Understanding Its Significance
Encryption is a fundamental force in the digital age, acting as a guardian of our private communications and sensitive data. […]