Semiconductors play a pivotal role in our daily lives, often going unnoticed yet fundamentally enabling the technology we rely on. […]
Author: admin
Blockchain Security Safeguarding Digital Transactions
Blockchain Security is revolutionizing the way we perceive and manage digital transactions. As the backbone of cryptocurrencies and various decentralized […]
Cloud Security A Comprehensive Guide to Protection
Cloud Security has become a pivotal aspect of our digital lives, shaping how we protect information in a world increasingly […]
Endpoint Protection Safeguarding Your Digital Assets
Endpoint Protection is not just a technological buzzword; it’s a crucial element in the defense against modern cyber threats that […]
Identity Access Management (IAM) Ensuring Security and Compliance
Kicking off with Identity Access Management (IAM), this vital framework serves as the backbone of security in modern enterprises, ensuring […]
Data Breach Understanding Causes and Prevention Strategies
Kicking off with Data Breach, it’s a term that resonates deeply in our increasingly digital lives. As organizations store more […]
Vulnerability Assessment Understanding Its Importance
Vulnerability Assessment plays a crucial role in today’s cybersecurity landscape, serving as the foundation for understanding and managing potential risks […]
Cryptography A Journey Through Time and Technology
Cryptography is an intriguing field that combines mathematics, computer science, and art to secure communication. As we navigate a world […]
Cyber Threat Intelligence Unraveling Cybersecurity Mysteries
Cyber Threat Intelligence serves as a crucial pillar in the modern cybersecurity landscape, equipping organizations with the insights needed to […]
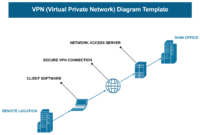
Virtual Private Network (VPN) Unveiling Its Benefits
Virtual Private Network (VPN) sets the stage for this enthralling narrative, offering readers a glimpse into a story that is […]